In This Article
Your Microsoft Secure Score reads 47%. The admin portal lists 60+ recommended actions sorted by point value. Some take five minutes. Some require weeks of planning and change management. The list does not tell you which ones actually reduce your risk versus which ones just raise the number.
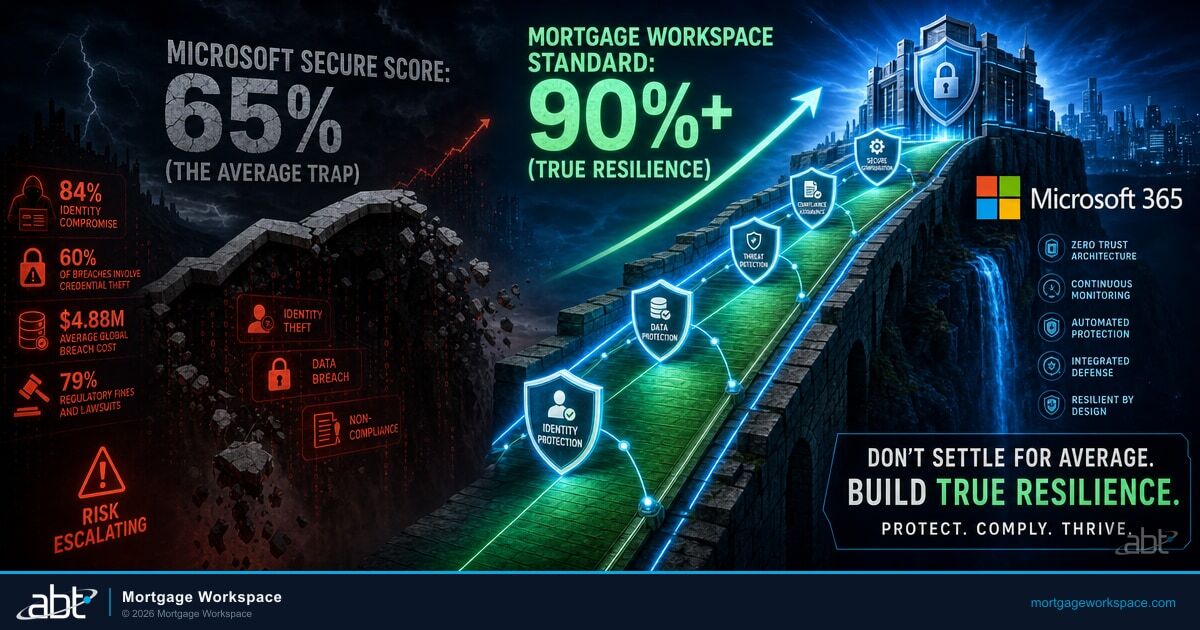
Financial institutions face a specific version of this problem. The IBM Cost of a Data Breach Report 2025 found that breaches in financial services cost an average of $5.56 million, second only to healthcare. Institutions that detected and contained breaches in under 200 days spent $3.87 million on average. Those that took longer spent $5.01 million. The gap between those two numbers is the gap between having a score and having a plan.
Guardian Security Insights closes that gap. It takes the raw Secure Score data and transforms it into a prioritized, sequenced action plan built for regulated financial institutions. Not a generic list of Microsoft recommendations. A roadmap where each action addresses real risk, produces compliance evidence, and moves the score toward 90%+ within 90 days.
IMAP, SMTP, POP3, and MAPI protocols disabled via Conditional Access policy
Every user has completed second-factor setup, not just started it
Accounts inactive 90+ days identified, disabled, and licenses reclaimed
MFA from untrusted locations, non-compliant device blocking, high-risk sign-in restrictions
Social Security numbers, bank accounts, and NPI protected across Exchange, SharePoint, OneDrive, and Teams
Configuration changes to Conditional Access, Intune, DLP, and Entra ID trigger immediate alerts
If your institution cannot check every box on that list, the gap between your current score and a defensible security program is wider than the number suggests. Guardian Security Insights builds the bridge.
Why Secure Score Alone Fails Financial Institutions
Microsoft Secure Score is a well-designed measurement tool. It is not a security program. Three limitations prevent it from driving real improvement at regulated financial institutions.
What Secure Score Tells You
- Point value for each recommended action
- Flat list of 60+ improvements
- Percentage across Identity, Data, Devices, Apps
- Microsoft's generic best practices
What Guardian SI Adds
- Risk-weighted priority based on your threat model
- Sequenced roadmap with prerequisites mapped
- Regulatory framework alignment (GLBA, FTC, FFIEC, NCUA)
- Financial-services-specific configuration standards
Point value does not equal risk reduction. Blocking legacy authentication might score fewer points than configuring advanced audit logging. But legacy authentication protocols like IMAP, SMTP, and POP3 cannot enforce MFA. The 2025 Verizon DBIR found that credential abuse caused 22% of all breaches. A mortgage lender holding borrower Social Security numbers and bank account data has a different risk profile than a consulting firm with the same number of Microsoft 365 users. Secure Score does not account for that difference.
No sequencing or dependencies. Microsoft presents recommended actions as a flat list. In practice, you cannot enforce device compliance through Conditional Access until devices are enrolled in Intune. You cannot require compliant devices until you define compliance policies. You cannot roll out MFA to all users simultaneously without a phased plan. A team that picks the highest-point action first may discover it requires three other changes they have not made.
No regulatory context. Secure Score recommendations align with Microsoft security best practices. They do not map to GLBA, FTC Safeguards Rule requirements, FFIEC examination expectations, NCUA ACET domains, or state regulations like NYDFS 23 NYCRR 500. With the FFIEC CAT sunsetting on August 31, 2025, and institutions transitioning to NIST CSF 2.0 or the CRI Profile, the regulatory landscape is shifting. Your IT director needs to know which Secure Score actions satisfy regulatory requirements and which are nice-to-have improvements above the compliance floor.
Where Does Your Tenant Actually Stand?
ABT's free Security Grade assessment shows you the gaps Secure Score misses.
The Guardian Security Insights Action Plan
Guardian Security Insights takes the raw Secure Score data and transforms it into a structured action plan. Every recommended action is reordered by actual risk, mapped to prerequisites, and aligned to the regulatory frameworks your examiners use.

Financial institutions with proactive security programs that detected and contained breaches in under 200 days spent $3.87 million on average, compared to $5.01 million for those exceeding 200 days. The 23% cost difference traces directly to prioritized remediation and continuous monitoring.
Here is how the action plan works across four phases.
Eliminate highest-risk gaps in weeks 1-2
Deploy Conditional Access, Intune, and DLP in weeks 3-6
Build continuous monitoring and drift detection in months 2-3
Maintain 90%+ and adapt to regulatory changes ongoing
Phase 1: Block the Biggest Threats (Weeks 1-2)
The first actions target the highest-risk gaps regardless of point value. For most financial institutions, these are:
Block legacy authentication. IMAP, SMTP, POP3, and MAPI protocols do not support MFA. Blocking them through a single Conditional Access policy removes the most exploited attack vector from your environment. Most lenders ABT onboards have legacy auth enabled because "someone might need it." ABT has yet to find that someone. If a specific application requires legacy auth, Guardian creates a scoped exception with monitoring rather than leaving the entire tenant exposed.
Complete MFA enrollment for all users. Not registration. Completion. Guardian Security Insights identifies every user who started MFA setup but never finished the second factor. Standard Microsoft reporting counts these users as MFA-enabled. They are not. Guardian's standard practice is to send enrollment completion links with a 48-hour deadline.
Disable stale accounts. Accounts inactive for 90+ days represent both security risk and budget waste. ABT recommends disabling them and reclaiming the licenses. Guardian Security Insights surfaces every stale account with the last login date, assigned roles, and license cost.
Phase 2: Harden the Configuration (Weeks 3-6)
With the biggest threats blocked, the next phase builds the security configuration that prevents drift.
- Deploy Conditional Access policies requiring MFA from untrusted locations, blocking non-compliant devices, and restricting high-risk sign-ins. Each policy maps to specific GLBA and FTC Safeguards Rule access control requirements.
- Enroll devices in Intune with compliance policies covering OS version, encryption, and screen lock. Block non-enrolled devices through Conditional Access. This gives your team visibility into every endpoint touching borrower data.
- Configure DLP policies that detect and protect Social Security numbers, bank account numbers, and other borrower data types in Exchange, SharePoint, OneDrive, and Teams. DLP is a GLBA requirement and an FTC Safeguards Rule expectation.
- Set up email authentication with SPF, DKIM, and DMARC to prevent domain spoofing. Phishing emails spoofing your loan officers' addresses cost borrowers money and cost your institution trust.
Phase 3: Build Monitoring and Reporting (Months 2-3)
With the hardened baseline in place, Guardian Security Insights shifts to continuous monitoring that catches changes before they become problems.
Enable Secure Score trending. Guardian Security Insights tracks your score across Identity, Data, Devices, and Apps with 30/60/90-day trend lines. A score that drops on Tuesday gets investigated on Wednesday, not discovered during the quarterly review.
Configure drift detection. Any modification to Conditional Access policies, Intune compliance rules, DLP configurations, or Entra ID settings triggers a logged event. Your team sees what changed, who changed it, and whether the change creates a compliance gap.
Build compliance reporting. Guardian Security Insights maps your current control state to every applicable regulatory framework. One data set, multiple audiences: your internal team, your auditor, your examiner, your cyber insurance carrier.
Phase 4: Optimize and Maintain (Ongoing)
Once your score stabilizes above 80% and trends toward 90%, the work shifts from implementation to optimization.
Guardian Security Insights evaluates each remaining Secure Score action against your risk profile and regulatory requirements. Some recommendations in the 80-100% range involve trade-offs. Microsoft adds new Secure Score actions quarterly. When NIST updates a control, when a state regulator issues new guidance, when your cyber insurance carrier changes their questionnaire, Guardian Security Insights maps the new requirements against your existing controls and identifies gaps before your next examination.
The 90-Day Roadmap: Score to Security Program
The pattern is consistent across the 750+ financial institutions ABT serves:
| Milestone | Typical Starting Point | After Guardian SI | Key Actions |
|---|---|---|---|
| Day 1 | Score: 35-55% | Baseline documented | Full tenant assessment, risk inventory |
| Day 30 | Legacy auth enabled, MFA gaps | Score jumps 20-30 points | Legacy auth blocked, MFA completed, stale accounts disabled |
| Day 60 | No Conditional Access, no DLP | Score above 75% | CA policies deployed, Intune enrolled, DLP active |
| Day 90 | No monitoring, no drift alerts | Score stabilizes 80%+, path to 90% | Continuous monitoring, compliance reporting, drift detection |
| 6 Months | Quarterly manual reviews | Maintenance rhythm | Prioritized daily reports, auto-generated audit evidence |
After six months, the security program operates on a maintenance rhythm. Your team works from prioritized daily reports. Auditors get evidence packages that answer their questions before they ask. Cyber insurance renewals include documentation that supports premium reduction conversations.

Beyond the Number: Metrics That Drive Real Security
Secure Score is one metric. Guardian Security Insights tracks the operational metrics that tell the full story of your security program.
A Secure Score of 85% with Identity at 95% and Devices at 60% is weaker than 85% with all four categories balanced. Examiners evaluate control coverage across domains, not a single aggregate number. Guardian Security Insights breaks the score into Identity, Data, Devices, and Apps with independent trend lines so your team and your examiner see the same picture.
- MFA completion rate: Percentage of users with fully enrolled (not just registered) MFA. Target: 100%. Guardian Security Insights tracks the gap between registered and enrolled.
- Stale account count: Number of accounts inactive beyond your policy threshold. Target: zero outside documented exceptions.
- Device compliance rate: Percentage of devices meeting all Intune compliance policies. Target: 95%+.
- Policy drift events per month: Unauthorized configuration changes detected. Trend should approach zero as governance matures.
- Mean time to remediate: Hours from detection to resolution. Guardian Security Insights clients with mature processes average under 48 hours for non-critical findings and under 4 hours for critical findings.
- Compliance gap count: Unresolved regulatory control gaps tracked against each applicable framework. Target: zero critical gaps, declining total gaps.
These metrics feed leadership dashboards and audit evidence packages. They tell two stories at once: your institution's security is improving, and you can prove it.
The attack surface has expanded with the evolution of new technologies and broadly-used remote access points, including mobile computing, smartphone applications, bring your own devices, and cellular connections.
FFIEC Authentication and Access Guidance
Pure Microsoft Architecture: Why It Matters
ABT is a cloud-first managed service provider and the largest Tier-1 Microsoft Cloud Solution Provider dedicated to financial services. ABT runs a pure Microsoft technology stack. No ConnectWise. No Kaseya. No SolarWinds. Guardian Security Insights is built on the same Microsoft tools your institution already licenses.
This architecture means Guardian Security Insights reads directly from your tenant's native APIs. No third-party data warehouse. No translation layer. No sync delays. The findings are as current as the data in your Microsoft 365 environment. When MSP platforms suffer breaches, ABT's architecture is completely unaffected because there is no third-party tooling in the chain.
ABT has managed Microsoft 365 tenants for financial institutions since 1999. Twenty-five years of configuration patterns, compliance requirements, and audit preparation across mortgage lenders, credit unions, banks, and regulated industries. Your institution's action plan is informed by that depth of experience. For a deeper look at how Guardian Security Insights sets higher standards than default Secure Score benchmarks, see our companion analysis.
Key Takeaway
Secure Score measures where you stand. Guardian Security Insights builds the roadmap to where you need to be. The difference between a number and a security program is sequencing, regulatory context, and continuous monitoring. All three come standard with the Guardian operating model.
Is Your Microsoft Secure Score Just a Number?
A Secure Score only matters when it drives action, and most lenders never translate it into a prioritized plan. MortgageWorkspace turns Guardian Security Insights into the specific Microsoft 365 changes that move the number and reduce real risk.
Frequently Asked Questions
Guardian Security Insights reorders raw Secure Score recommendations by actual risk rather than point value. Each action is sequenced with prerequisites, mapped to regulatory frameworks including GLBA and FTC Safeguards Rule, and assigned estimated effort. The result is a phased roadmap starting with highest-risk gaps and building toward 90%+ across all four score categories.
Most financial institutions start between 35% and 55%. After blocking legacy authentication, completing MFA enrollment, and disabling stale accounts, scores typically jump 20-30 points in the first month. By 90 days, scores stabilize above 80% with a clear path to 90%+. Continuous monitoring and optimization maintain the score from that point forward.
Legacy authentication protocols like IMAP, SMTP, and POP3 cannot enforce multi-factor authentication, making them the primary entry point for credential-based attacks. The 2025 Verizon DBIR found credential abuse caused 22% of all breaches. Blocking legacy auth through a single Conditional Access policy removes this attack vector entirely within the first week of onboarding.
With the FFIEC CAT sunsetting August 31, 2025, institutions must transition to frameworks like NIST CSF 2.0 or the CRI Profile. Guardian Security Insights maps Secure Score controls directly to these successor frameworks, providing continuous alignment documentation that satisfies examiner expectations during and after the transition period.
Guardian Security Insights tracks MFA completion rate, stale account count, device compliance percentage, policy drift events per month, mean time to remediate findings, and compliance gap count per regulatory framework. These operational metrics provide the visibility that Secure Score alone cannot deliver and produce the evidence auditors and examiners expect.
Your Score Is a Starting Point. Your Security Program Starts Here.
The 750+ financial institutions ABT serves moved from static Secure Scores to prioritized action plans with Guardian Security Insights. See where your tenant stands in under 5 minutes.

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch has led security posture management programs for regulated financial institutions since 1999. As CEO of Access Business Technologies, the largest Tier-1 Microsoft Cloud Solution Provider dedicated to financial services, he helps more than 750 banks, credit unions, and mortgage companies transform Microsoft Secure Score from a static metric into a defensible security program through Guardian Security Insights.