In this article:
- Why Email Is the #1 Attack Vector for Mortgage Fraud
- Wire Fraud in Real Estate: How Attacks Actually Work
- Business Email Compromise: How Attackers Target Your Closing Process
- SPF, DKIM, and DMARC: The Email Authentication Foundation
- Microsoft 365 Email Security Settings Every Mortgage Company Needs
- Wire Transfer Verification: Process Controls Beyond Technology
- Incident Response: When a Phishing Attack Gets Through
- Frequently Asked Questions
In 2024, the FBI's Internet Crime Complaint Center recorded $2.77 billion in losses from Business Email Compromise attacks across 21,442 reported incidents. Real estate transactions accounted for over 2,100 of those cases, with losses exceeding $312 million.
Mortgage companies sit at the intersection of the two things attackers want most: large wire transfers and time pressure. A typical closing involves multiple parties exchanging wiring instructions over email, often within hours of the funding deadline. One spoofed email with modified bank routing numbers can redirect a $400,000 wire to an account controlled by the attacker.
This isn't a hypothetical scenario. It happens to mortgage companies, title agencies, and settlement firms every week. The FBI investigated over 9,359 real estate fraud complaints in 2024, and the actual number is higher because most incidents go unreported.
This article covers the technical email security controls, Microsoft 365 configurations, and process safeguards that mortgage operations need to stop wire fraud and BEC attacks before they reach the closing table.
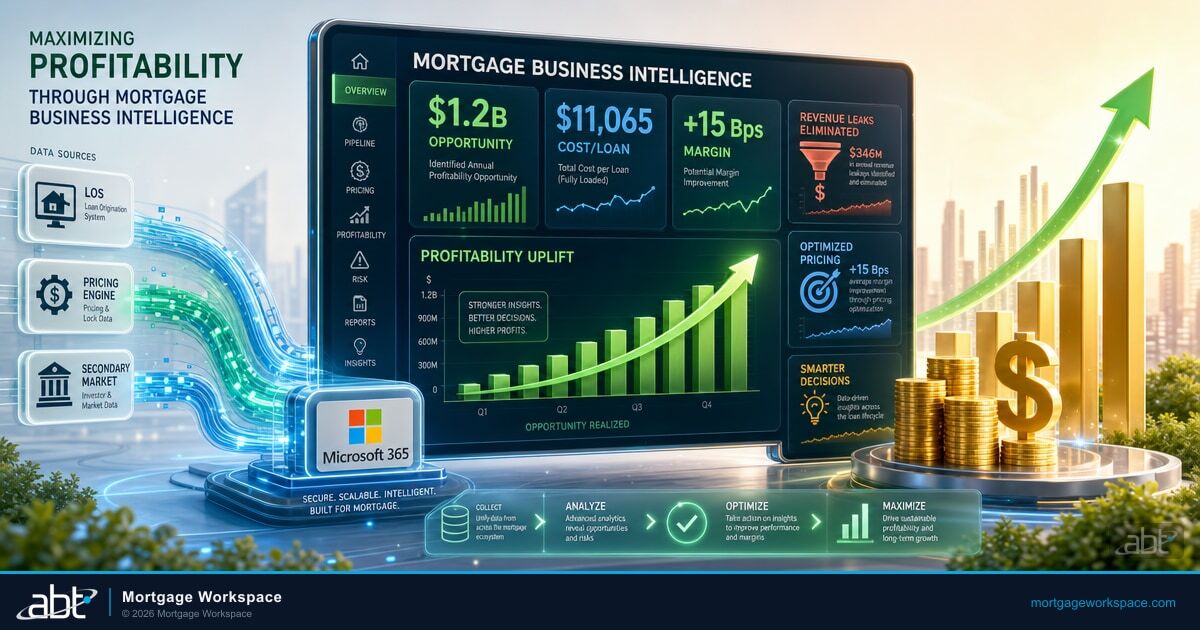
How ABT Stops Wire Fraud at the Closing Table
Access Business Technologies is a Tier-1 Microsoft Cloud Solution Provider managing Microsoft 365 tenants for 750+ financial institutions, including independent mortgage banks, mortgage brokers, and hybrid lending operations. The stack that actually stops BEC and wire fraud in this footprint is the same stack ABT operates as managed services: M365 Guardian is the configuration and monitoring layer that hardens every tenant against the controls described in this article; Microsoft Defender for Office 365 handles Safe Links, Safe Attachments, anti-phishing impersonation, and inbox-rule alerting at the email gateway; and Microsoft Sentinel correlates signals across email, identity, and endpoint to surface the multi-step BEC patterns that any single tool would miss.
The reason this stack works for mortgage closings is operational. A title company impersonation attempt does not show up as one bad email. It shows up as a credential phish on Monday, an inbox-rule creation on Tuesday, a lookalike-domain registration on Wednesday, and a fraudulent wire instruction on Thursday. ABT runs these tools as a continuous monitoring function tied to the closing workflow, with anti-phishing and impersonation policies tuned to the title-company domains your team actually communicates with, mailbox-audit alerts on inbox-rule creation, and Sentinel analytic rules tuned to the wire-fraud attack chain. The mortgage company experiences the outcomes: a configured tenant, alerts that fire on the right signals, and an operational owner who answers the phone when an examiner asks for evidence of email security controls.
Why Email Is the #1 Attack Vector for Mortgage Fraud
The mortgage closing process was built on email. Loan officers email rate locks to borrowers. Title companies email closing disclosures. Settlement agents email wiring instructions. Every one of those emails is a potential attack surface.
Three factors make mortgage email traffic uniquely attractive to attackers:
High-value transactions on predictable timelines. A residential mortgage closing typically involves a wire transfer between $50,000 and $500,000. Commercial closings can exceed $10 million. Attackers know these wires are coming because closing dates are public record in many jurisdictions, and the timeline creates urgency that overrides caution.
Multiple parties with weak security posture. A single closing can involve the borrower, loan officer, processor, closer, title company, real estate agents on both sides, and an attorney. The attacker only needs one compromised mailbox in that chain. If the title company's email lacks DMARC enforcement, an attacker can send wiring instructions that pass basic email checks.
Time pressure that suppresses verification. When a closer calls to say "we need the wire by 2 PM or we lose the rate lock," nobody wants to slow things down with a callback to verify routing numbers. Attackers exploit this urgency deliberately. They time their fraudulent emails to arrive during the most chaotic phase of the closing.
The FinCEN data backs this up. Wire transfer Suspicious Activity Reports filed by financial institutions grew 40% between 2022 and 2024, from 136,000 to 188,000 filings. Wire SARs have posted three consecutive years of double-digit growth: 32%, 26%, and 24%. And the frequency is accelerating. Financial institutions now file one SAR for every 2,899 wire transfers, compared to one for every 8,636 wires in 2015.
Compliance Starts with Measurement
Your security configuration is only as strong as your last review. ABT evaluates Conditional Access, MFA, sensitivity labels, and sharing policies against regulatory benchmarks.
Wire Fraud in Real Estate: How Attacks Actually Work
Wire fraud in mortgage transactions follows a consistent pattern. Understanding the attack chain is the first step to breaking it.

Step 1: Reconnaissance. The attacker identifies an active transaction. Public property records, MLS listings, and social media posts from real estate agents ("Just went under contract!") all signal that a closing is coming. Some attackers monitor compromised email accounts for weeks before acting, reading every message to learn the participants, timeline, and communication patterns.
Step 2: Email compromise. The attacker gains access to one party's email account, usually through credential phishing or password spraying. Title companies and real estate agents are the most common targets because they handle multiple transactions and often lack enterprise-grade email security. A single compromised mailbox gives the attacker visibility into dozens of active closings.
Step 3: Observation. Once inside the mailbox, the attacker sets up inbox rules to forward specific emails (anything containing "wire," "closing," "settlement," or "funds") to an external address. They study the communication patterns: who emails whom, what the standard wiring instruction format looks like, how the sender signs off.
Step 4: The redirect. Hours before the scheduled wire, the attacker sends modified wiring instructions. The email comes from the compromised account (or a spoofed lookalike domain like "ti1tecompany.com" instead of "titlecompany.com"), uses the correct formatting, references the correct property address and closing date, and changes only the routing and account numbers. The new account is typically at a domestic bank, chosen because domestic wires clear faster than international transfers.
Step 5: Extraction. Within minutes of the wire hitting the fraudulent account, the funds are moved again, often split across multiple accounts or converted to cryptocurrency. The FBI's Financial Fraud Kill Chain froze $469 million in domestic fraudulent transfers in 2024 with a 66% success rate, but that window is narrow. Once funds leave the initial receiving account, recovery drops sharply.
Here's a specific scenario that plays out regularly:
A borrower is closing on a $380,000 home. Two days before closing, they receive an email from what appears to be their title company with updated wiring instructions. The email uses the correct title company logo, references the property address, and matches the format of previous legitimate emails. The only difference: the routing and account numbers point to a bank account in Texas controlled by the attacker. The borrower wires $76,000 for the down payment. By the time the title company contacts the borrower on closing day to ask where the wire is, the funds have already been moved through three accounts and partially converted to cryptocurrency. The borrower's entire down payment is gone.
This is not an edge case. The FBI investigated over 2,100 real estate BEC cases with this pattern in 2024. First-time homebuyers are victimized at three times the rate of experienced buyers, according to CertifID's 2025 State of Wire Fraud report.
Business Email Compromise: How Attackers Target Your Closing Process
BEC attacks targeting mortgage companies go beyond simple spoofed emails. Modern BEC operations are structured campaigns that combine technical exploitation with social engineering.
Lookalike domain attacks. The attacker registers a domain that's visually similar to the target: "mortgageworkspace.com" becomes "rnortgageworkspace.com" (the "m" replaced with "rn"). They configure SPF and DKIM on the lookalike domain so the fraudulent email actually passes authentication checks. The recipient's email client shows a green checkmark. The only tell is the domain name itself, and most people don't read it character by character.
Compromised vendor chains. Rather than targeting the mortgage company directly, attackers compromise a vendor in the closing chain. Title companies, appraisers, and settlement agents are frequent entry points because they often have smaller IT teams and weaker email controls. Once inside, the attacker can send legitimate-looking instructions to every party in every active closing that vendor handles.
Thread hijacking. The attacker gains access to a real email thread about a real closing and replies within that thread with modified wiring instructions. Because the message appears in an existing conversation, the recipient has no reason to question its authenticity. The "from" address is correct because the attacker is using the actual compromised account.
AI-generated pretexts. In 2024 and 2025, attackers began using generative AI to produce more convincing phishing emails. The awkward grammar and formatting errors that used to be red flags are disappearing. AI-generated emails match the tone and vocabulary of the person being impersonated, making them harder to distinguish from legitimate communications.
SPF, DKIM, and DMARC: The Email Authentication Foundation
Email authentication is the technical foundation that prevents attackers from sending emails that impersonate your domain. Three protocols work together: SPF verifies the sending server, DKIM verifies the message hasn't been altered, and DMARC tells receiving servers what to do when emails fail those checks.
SPF (Sender Policy Framework) publishes a DNS record listing every IP address and server authorized to send email on behalf of your domain. When a receiving server gets an email claiming to be from yourmortgagecompany.com, it checks the SPF record. If the sending server isn't listed, SPF fails. For mortgage companies using Microsoft 365, the SPF record needs to include Microsoft's sending infrastructure plus any third-party services that send email on your behalf (marketing platforms, CRM systems, loan origination system notifications).
DKIM (DomainKeys Identified Mail) adds a cryptographic signature to every outgoing email. The sending server signs the message with a private key, and the receiving server verifies it against a public key published in your DNS. If an attacker intercepts and modifies the message (changing wire instructions, for example), the DKIM signature breaks. DKIM has a 96.6% validity rate among properly configured domains, but only 22.7% of domains globally have DKIM implemented at all.
DMARC (Domain-based Message Authentication, Reporting & Conformance) is the enforcement layer. It tells receiving email servers what to do when an email fails SPF and DKIM checks: monitor it (p=none), quarantine it (p=quarantine), or reject it outright (p=reject). DMARC also generates reports showing who is sending email using your domain, which is how you discover unauthorized senders.
The problem: adoption is dangerously low. Only 43% of banking and financial services organizations have achieved DMARC enforcement, according to Valimail's Banking DMARC Enforcement Report. Globally, 71% of domains have no effective DMARC protection. Only 10.7% of all domains worldwide are at full DMARC enforcement with a reject policy.
For mortgage companies specifically, that gap is a direct path to wire fraud. If your domain doesn't have DMARC at p=reject, an attacker can send emails that appear to come from your domain, and the recipient's email server has no instruction to block them.
Email Security Quick Check: 5 Critical Settings to Verify Today
- SPF record published and valid: Check your DNS for a TXT record starting with "v=spf1" that includes all authorized senders (Microsoft 365, CRM, LOS notifications). Use mxtoolbox.com/spf.aspx to validate.
- DKIM enabled and signing: In Microsoft 365 Defender, verify DKIM is enabled for your domain under Email Authentication Settings. Both CNAME records must be published in DNS.
- DMARC at enforcement (p=quarantine or p=reject): Check your DNS for a TXT record starting with "v=DMARC1". If the policy is "p=none," you're monitoring but not blocking. Move to p=quarantine, then p=reject.
- Anti-phishing policies configured: In Microsoft 365 Defender, verify anti-phishing policies include impersonation protection for your executives and key domains (title companies, settlement agents).
- External email warning banner enabled: Configure a mail flow rule that prepends "[EXTERNAL]" to the subject or adds a visible banner to every email received from outside your organization.
Microsoft 365 Email Security Settings Every Mortgage Company Needs
Most mortgage companies run their email on Microsoft 365. The platform includes email security features inside Microsoft Defender for Office 365 that can stop BEC and phishing attacks, but many of them are turned off by default or require specific configuration. ABT operates these settings as part of M365 Guardian on every managed tenant, with anti-phishing impersonation lists tuned to the title companies and settlement agents each customer actually closes with. For mortgage operations managing their own tenant, the configuration below is the baseline. For an operational view of how mortgage companies build a security program around these controls, see Beyond Microsoft Secure Score: Building a Mortgage Operations Security Program.
1. Enable Safe Links for real-time URL scanning. Safe Links is a Microsoft Defender for Office 365 feature that rewrites URLs in incoming emails and checks them at the time of click, not just at delivery. This catches time-delayed attacks where the attacker sends a clean URL that redirects to a phishing site hours later. In the Microsoft 365 Defender portal, create a Safe Links policy that covers all users and enable "Wait for URL scanning to complete before delivering the message."
2. Enable Safe Attachments with Dynamic Delivery. Safe Attachments opens email attachments in a sandboxed environment before delivering them. Dynamic Delivery lets the email body through immediately while the attachment is being scanned, so users aren't waiting for every email. Enable this for all mailboxes, especially those involved in closing operations.
3. Configure anti-phishing impersonation protection. Microsoft 365 Defender's anti-phishing policies can detect when someone is impersonating specific users or domains. Add your CEO, CFO, closing managers, and any title company domains your team regularly communicates with to the protected senders and domains list. Set the action to quarantine messages that trigger impersonation detection.
4. Block legacy authentication protocols. Legacy protocols (POP3, IMAP with basic auth, SMTP AUTH) don't support multi-factor authentication, making them easy targets for credential stuffing. Create a Conditional Access policy in Entra ID that blocks legacy authentication for all users. This is one of the highest-impact security changes you can make, and it costs nothing.
5. Enable Security Defaults or Conditional Access MFA. Every user who touches closing-related email must have MFA enabled. Security Defaults is the baseline (free with any M365 plan). For mortgage companies, Conditional Access policies offer more control: require MFA for all sign-ins from unmanaged devices, block sign-ins from countries where you don't do business, and require compliant devices for access to Exchange Online.
6. Configure Mailbox Audit Logging. Verify that mailbox auditing is enabled (it's on by default in M365 but some tenants have it disabled). Audit logs capture when someone creates inbox rules, accesses mailbox contents, or sends email as another user. These logs are how you detect an attacker who has compromised an account and is silently forwarding closing-related emails.
7. Set up alerts for suspicious inbox rules. BEC attackers almost always create inbox rules to hide their activity. Configure an alert in Microsoft Defender for Office 365 that triggers when any user creates a rule that forwards or redirects email to an external address. This is one of the earliest indicators of a compromised account. ABT-managed tenants extend this baseline by feeding inbox-rule events into Microsoft Sentinel, where analytic rules correlate the rule-creation signal with other indicators on the same account (anomalous sign-in geography, MFA-bypass attempts, lookalike-domain email traffic) to surface the full BEC attack chain rather than a single isolated event.
8. Enable tenant-wide external email tagging. Configure Exchange Online to prepend a visible warning to every email from outside your organization. The message should be unmistakable: "CAUTION: This email originated from outside your organization. Verify the sender before clicking links or following wire instructions." This is a simple visual cue that reminds staff to verify before acting on wiring instructions. For the broader configuration baseline this layer sits inside, see Best Practices for Configuring Microsoft 365 Email for Mortgage Offices.
Wire Transfer Verification: Process Controls Beyond Technology
Email security controls reduce the chance of a fraudulent email reaching your team. But technology alone isn't enough. The mortgage companies that avoid wire fraud combine email security with process controls that work even when a phishing email gets through.

Verbal callback verification on every wire. Before processing any wire transfer, the closer or funding coordinator must call the recipient using a phone number obtained independently, not from the wiring instructions themselves. Use the number on file from the initial onboarding of the title company or settlement agent. Never use a phone number from the same email that contains the wiring instructions.
Dual-authorization for wires above a threshold. Any wire over a set amount (many mortgage companies use $10,000) requires approval from two authorized individuals. This prevents a single compromised employee from redirecting funds.
Wiring instruction change protocol. If wiring instructions change at any point during the closing process, treat it as a red flag until proven otherwise. The change must be verified by phone callback to a known number, documented in the loan file, and approved by a manager. Changed wiring instructions close to the funding deadline should receive extra scrutiny.
Borrower education at application. At the time of application, provide every borrower with a written notice explaining that your company will never send wiring instructions by email without a confirming phone call. Include the specific phone number they should call to verify any wiring instructions they receive. This sets the expectation early, before the time pressure of closing day.
Title company and vendor vetting. Before adding a title company or settlement agent to your approved vendor list, verify their email security posture. At minimum: do they have DMARC at enforcement? Do they require MFA for all employees? Have they had a wire fraud incident in the past two years? These questions should be part of your vendor due diligence process.
FBI IC3 2024 Annual Report; CertifID State of Wire Fraud 2025"The FBI investigated over 2,100 real estate BEC cases in 2024 with total losses exceeding $312 million. First-time homebuyers were victimized at three times the rate of experienced buyers."
Incident Response: When a Phishing Attack Gets Through
Even with strong email security and process controls, some attacks will get through. Your incident response plan determines whether a successful phishing email becomes a contained event or a six-figure loss. On ABT-managed tenants, the steps below are coordinated by the M365 Guardian operations team with Microsoft Sentinel as the investigation surface. Sign-in logs, mailbox audit events, and Defender for Office 365 detections are pre-joined in the SIEM so the root-cause analysis takes hours, not days. For loan files and borrower documents that move through the closing process alongside email, the document-security controls in Document Security for Remote Mortgage Teams sit alongside this playbook.
Immediately (within 15 minutes of discovery):
- Disable the compromised account. Reset the password and revoke all active sessions in Entra ID.
- Check inbox rules on the compromised account. Delete any rules forwarding or redirecting email to external addresses.
- If a fraudulent wire was sent, contact your bank's wire fraud department immediately. The FBI's Financial Fraud Kill Chain has a 66% success rate for freezing domestic fraudulent transfers, but only if the bank is notified within 24 hours.
- File a complaint with the FBI IC3 at ic3.gov. This starts the recovery process and feeds federal tracking data.
Within 1 hour:
- Notify all parties in the affected transaction(s) that the account was compromised. Every borrower, agent, and vendor who communicated with the compromised mailbox needs to know.
- Review the audit logs. Determine when the compromise started, what the attacker accessed, and whether inbox rules were created to monitor other active closings.
- Check for lateral movement. Did the attacker use the compromised account to send phishing emails to other employees or external parties?
Within 24 hours:
- Complete a full sign-in log review for the compromised user. Identify any unusual locations, IP addresses, or devices.
- Notify your cyber insurance carrier. Most policies require notification within 24-72 hours.
- Determine regulatory notification requirements. State data breach notification laws vary, and CFPB, state regulators, and GSE requirements may apply depending on the scope of the compromise.
- Conduct a company-wide credential review. If one account was compromised via credential phishing, others may be at risk.
Within 1 week:
- Complete a root cause analysis. How did the attacker gain access? Which control failed? What would have stopped this attack?
- Update your email security configuration based on findings. If the attack exploited a gap in anti-phishing policy, fix it.
- Conduct targeted security awareness training for the affected team, focusing on the specific attack pattern that succeeded.
- Document the incident for your CFPB exam file and cyber insurance renewal.
“Every examination we prepare institutions for reveals the same pattern: the controls exist, but the configuration doesn’t match the policy. That gap is where examiners focus - and where breaches happen.”
Serving 750+ financial institutions since 1999
Stop Guessing About Your Email Security Posture
ABT operates M365 Guardian, Microsoft Defender for Office 365, and Microsoft Sentinel as managed services for 750+ financial institutions. Get an architect-led review of your tenant configuration against the BEC and wire-fraud control set in this article. Close the gap in 48 hours.
Frequently Asked Questions
Business Email Compromise (BEC) is the most common and most costly email attack targeting mortgage companies. BEC attacks typically involve an attacker gaining access to a legitimate email account or spoofing a trusted domain to send fraudulent wiring instructions during the closing process. The FBI recorded $2.77 billion in BEC losses across all industries in 2024, with over 2,100 cases specifically involving real estate transactions and losses exceeding $312 million.
DMARC prevents attackers from sending emails that impersonate your domain. When configured at enforcement level (p=quarantine or p=reject), DMARC instructs receiving email servers to block or quarantine emails that fail SPF and DKIM authentication checks. This stops an attacker from sending fraudulent wiring instructions that appear to come from your mortgage company's domain. However, only 43% of banking and financial services organizations have achieved DMARC enforcement, leaving the majority vulnerable to domain spoofing.
Mortgage companies on Microsoft 365 should enable Safe Links for real-time URL scanning, Safe Attachments with Dynamic Delivery, anti-phishing impersonation protection for key personnel and partner domains, external email warning banners, and alerts for suspicious inbox rule creation. They should also block legacy authentication protocols through Conditional Access and require multi-factor authentication for all users who handle closing-related email.
If a fraudulent wire transfer is sent, immediately contact your bank's wire fraud department to request a recall. File a complaint with the FBI IC3 at ic3.gov within 24 hours, as the FBI's Financial Fraud Kill Chain achieved a 66% success rate in freezing domestic fraudulent transfers in 2024. Simultaneously, disable the compromised email account, revoke all active sessions, check for inbox forwarding rules, and notify all parties in the affected transaction. Contact your cyber insurance carrier within the policy's notification window, typically 24 to 72 hours.
Every wiring instruction should be verified by phone callback using a number obtained independently from the wiring instructions email. Use the phone number on file from the initial vendor onboarding, never a number from the email containing the wire details. Implement dual-authorization for wires above a set threshold, treat any change in wiring instructions as a red flag requiring manager approval, and educate borrowers at application about your verification process so they know what to expect.
While no mortgage-specific regulation mandates DMARC, PCI DSS v4.0.1 requires anti-phishing and anti-spoofing controls (Requirement 5.4.1), which DMARC, SPF, and DKIM satisfy, for organizations that process payment card data, effective March 31, 2025. Industry guidance and examination trends point toward demonstrable email security controls as part of information security programs. GSE seller/servicer guides (Fannie Mae and Freddie Mac) require information security programs that would reasonably include email authentication. DMARC enforcement is rapidly becoming a baseline expectation in regulatory examinations.

Justin Kirsch
Justin Kirsch has spent over two decades protecting mortgage operations from email-based attacks. As CEO of Access Business Technologies, his team has implemented email security configurations for hundreds of mortgage companies, directly preventing wire fraud attempts and business email compromise attacks that target the closing process.