In this article:
The FBI logged over 859,000 internet crime complaints in 2024 with reported losses exceeding $16 billion. Financial services phishing accounts for 27.7% of all phishing attempts. For mortgage offices handling Social Security numbers, bank statements, and loan applications, email is the primary attack surface.
Microsoft 365 provides the tools to lock it down. But the default configuration is not enough. Proper setup requires mortgage-specific policies, data loss prevention rules tuned to borrower information, and authentication hardening that meets the FTC Safeguards Rule.
Why Microsoft 365 Is the Standard for Mortgage Email
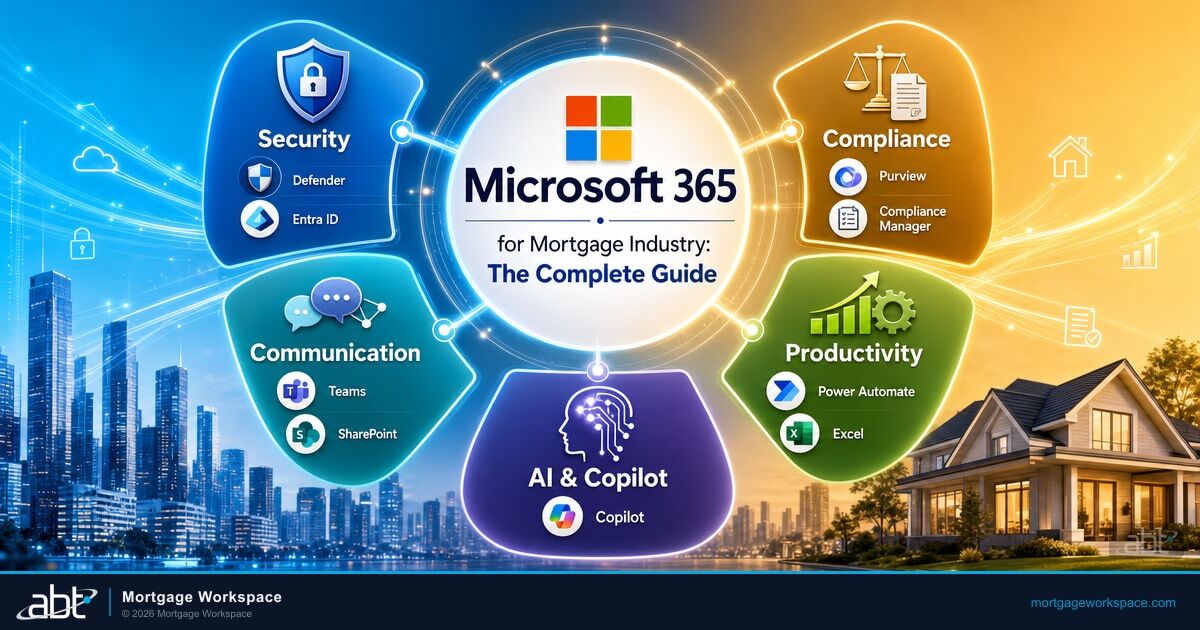
Microsoft 365 is more than an inbox. It is a compliance-ready platform with built-in security controls that map directly to mortgage regulatory requirements.
Built-In Compliance and Security
Mortgage offices handle vast amounts of sensitive financial information. Microsoft 365 ships with encryption, advanced threat protection through Defender for Office 365, and compliance frameworks that align with GLBA, SOC 2, and ISO 27001. Microsoft Purview Compliance Manager includes a regulatory template specifically for GLBA and the FFIEC Information Security Booklet.
Real-Time Collaboration Without Compliance Risk
Loan officers and processors share documents throughout the origination process. OneDrive and SharePoint provide secure file storage with version history and access controls. Microsoft Teams replaces unsecured email threads for internal coordination. Every document edit is tracked, creating audit trails that survive regulatory review.
Access from Anywhere, Secured Everywhere
Remote and hybrid work is standard in mortgage operations. Microsoft 365's cloud-based access works across desktop, tablet, and mobile. Conditional Access policies in Entra ID restrict access based on device compliance, location, and risk level. A loan officer reviewing documents from home gets the same security enforcement as someone in the office.
Integration with Mortgage Software
Microsoft 365 connects with loan origination systems like Encompass and Calyx through APIs and Power Automate workflows. Borrower communications, document routing, and compliance notifications can flow through a unified platform rather than disconnected point solutions.
Step-by-Step Configuration for Mortgage Offices
Getting the basics right prevents most email-based incidents. These steps apply to any mortgage office running Microsoft 365 Business Premium or higher.
1. Set Up Individual User Accounts
- Dedicated accounts for every team member. Loan officers, processors, and managers each get their own Microsoft 365 account. Shared logins destroy audit trails and violate the FTC Safeguards Rule's access control requirements.
- Distribution lists for team communication. Create lists like loanprocessing@yourcompany.com for internal routing. Keep borrower-facing communications on individual accounts for traceability.
- Delegated permissions where needed. Support inboxes and shared mailboxes use delegate access, not shared passwords. Every action ties back to a specific user.
2. Configure Email Security
- Enable Defender for Office 365 anti-phishing policies. Configure impersonation protection for key personnel like your CEO, CFO, and controller. Targeted phishing attacks impersonate executives to authorize wire transfers.
- Set up Data Loss Prevention (DLP) rules. Create policies that detect Social Security numbers, bank account details, and loan application data in outbound emails. DLP rules alert employees before sensitive borrower information leaves your organization through unencrypted channels.
- Enable message encryption. Outlook Message Encryption ensures loan documents and borrower correspondence stay confidential in transit. Recipients outside your organization open encrypted emails through a secure portal.
- Deploy SPF, DKIM, and DMARC. These email authentication protocols prevent attackers from spoofing your company domain. DMARC enforcement tells receiving mail servers to reject emails that fail authentication checks.
3. Implement Multi-Factor Authentication
The FTC Safeguards Rule requires MFA for anyone accessing customer information. This includes desktop access, not just web applications.
Deploy Microsoft Authenticator for push-based MFA at minimum. For high-risk accounts like administrators and finance personnel, implement FIDO2 security keys that resist phishing proxy attacks. The NYDFS Part 500 amendments require universal MFA for all system access with first certification due April 2026.
Best Practices for Email Management
Establish Retention Policies
Mortgage offices must retain emails for legal and regulatory compliance. Configure Microsoft 365 retention policies to archive emails automatically based on content type and age. GLBA and state regulations specify minimum retention periods. Automated policies prevent accidental deletion and reduce storage clutter.
Run Monthly Security Audits
Cybersecurity is not a one-time configuration.
- Review Secure Score recommendations in the Microsoft 365 admin center monthly.
- Audit administrator privileges quarterly. Remove accounts that no longer need elevated access.
- Check for inactive accounts and deactivate them. Dormant accounts are attack targets.
- Review email forwarding rules. Unauthorized forwarding rules are a hallmark of compromised accounts.
Train Staff with Real Phishing Simulations
32% of employees fall for phishing scams without proper training. Annual compliance videos do not change behavior. Monthly phishing simulations using Microsoft's Attack Simulation Training give staff hands-on experience spotting targeted emails. Scenarios should include invoice fraud, vendor portal updates, and wire transfer requests specific to mortgage workflows.
Integrate with Mortgage-Specific Tools
- DocuSign or Adobe Sign for secure electronic signatures on loan documents directly through Outlook.
- Power Automate workflows that route loan status updates, compliance reminders, and borrower notifications without manual email handling.
- Guardian Insights from Mortgage Workspace provides security reporting and productivity analysis layered on top of the Microsoft 365 environment.
Why Secure Email Is Non-Negotiable
The average cost of a data breach in financial services is $4.4 million. For a mid-size mortgage company, that figure can mean closure.
In November 2025, the SitusAMC breach exposed mortgage loan data across hundreds of financial institutions through a single vendor compromise. The attack vector: unauthorized access to systems that processed email, documents, and accounting records. Every mortgage office that relied on that vendor's security was exposed.
Properly configured Microsoft 365 email reduces this risk at every layer. Encryption protects data in transit. DLP prevents accidental exposure. Conditional Access restricts who can reach your systems. Defender catches threats before they reach inboxes.
But configuration alone is not the full picture. Ongoing monitoring, policy tuning, and incident response require dedicated expertise.
Get Your Email Configuration Right the First Time
Mortgage Workspace, backed by Access Business Technologies, is a Tier-1 Microsoft Cloud Solution Provider serving 750+ financial institutions. We configure, manage, and monitor Microsoft 365 environments built specifically for mortgage compliance.
Guardian, ABT's proprietary control layer, handles tenant hardening, email authentication enforcement, DLP policy management, and continuous compliance drift detection. No third-party MSP platforms in the stack. No added supply chain risk.
Talk to a mortgage IT specialist to get your Microsoft 365 email environment assessed and hardened for compliance.
Related Articles
- Document Security for Remote Mortgage Teams: Best Practices for Data Protection
- Interface Security Best Practices for Mortgage Application Platforms
- Bridging IT and Compliance in the Mortgage Industry with Microsoft Solutions
Frequently Asked Questions
What email security settings does the FTC Safeguards Rule require for mortgage lenders?
The FTC Safeguards Rule requires mortgage lenders to encrypt customer information in transit and at rest, implement multi-factor authentication for anyone accessing customer data including desktop and server access, conduct regular penetration testing of applications that handle customer information, and maintain access controls that are periodically reviewed. Lenders must also deploy monitoring and logging to track user activity and detect unauthorized access to email systems containing borrower data.
How do Data Loss Prevention rules in Microsoft 365 protect borrower information?
Data Loss Prevention rules in Microsoft 365 scan outbound emails and attachments for patterns matching sensitive data types like Social Security numbers, bank account numbers, and credit card details. When a match is detected, the policy can block the email, require encryption, or notify the sender with a warning before the message is sent. Mortgage offices configure custom DLP policies tuned to loan application data types to prevent accidental disclosure of borrower information to unauthorized recipients.
Why should mortgage offices use SPF, DKIM, and DMARC for email authentication?
SPF, DKIM, and DMARC are email authentication protocols that prevent attackers from spoofing your company domain in phishing emails. SPF verifies the sending server is authorized. DKIM adds a digital signature that confirms the email was not altered in transit. DMARC ties SPF and DKIM together with a policy that tells receiving servers to reject or quarantine emails that fail authentication. For mortgage companies, domain spoofing is a primary vector for wire fraud and business email compromise schemes.
What is Microsoft Purview Compliance Manager and how does it help mortgage companies?
Microsoft Purview Compliance Manager provides a compliance score for your organization and offers regulatory assessment templates for frameworks including GLBA, FFIEC, and the FTC Safeguards Rule. It identifies gaps in your current configuration, recommends specific improvement actions, and tracks progress toward compliance targets. For mortgage companies, Compliance Manager maps Microsoft 365 settings directly to regulatory requirements and generates documentation useful during audits and examinations.