In This Article
Financial services was the most breached industry in 2025 for the third consecutive year, with 739 reported data compromises according to the ITRC's Annual Data Breach Report. Mortgage companies sit at the center of that target because they collect everything attackers want: Social Security numbers, credit reports, bank account details, and income records.
The Marquis Software Solutions breach in August 2025 proved how fast damage spreads. A single vendor compromise exposed sensitive data from over 700 financial institutions. That vendor paid a ransom, which triggered OFAC sanctions exposure and FinCEN SAR filing requirements for every affected lender.
Microsoft 365 isn't just email and spreadsheets. Its security stack includes threat detection, encryption, access controls, and compliance tools built for regulated industries. This guide covers what those tools do and how credit unions, banks, and mortgage companies should deploy them.
The Mortgage Cybersecurity Threat Landscape in 2026
Mortgage companies handle personally identifiable information at every stage of the loan lifecycle. From application through servicing, borrower data flows between loan officers, processors, underwriters, and third-party vendors.
Three attack vectors dominate in 2026:
Phishing and business email compromise — attackers impersonate title companies, real estate agents, or executives to redirect wire transfers. Ransomware targeting vendors — supply chain attacks through third-party vendors are the fastest-growing vector in financial services. Remote work exposure — loan officers accessing sensitive data from personal devices and unsecured networks.
The Marquis Software Solutions breach exposed data from 700+ financial institutions through a single vendor compromise. The Clop ransomware group targeted a Canadian mortgage firm in February 2026, threatening to expose borrower data. Every attack on a mortgage vendor cascades to its customers — your security is only as strong as your weakest vendor connection.

Why Securing Mortgage Data Is Getting Harder
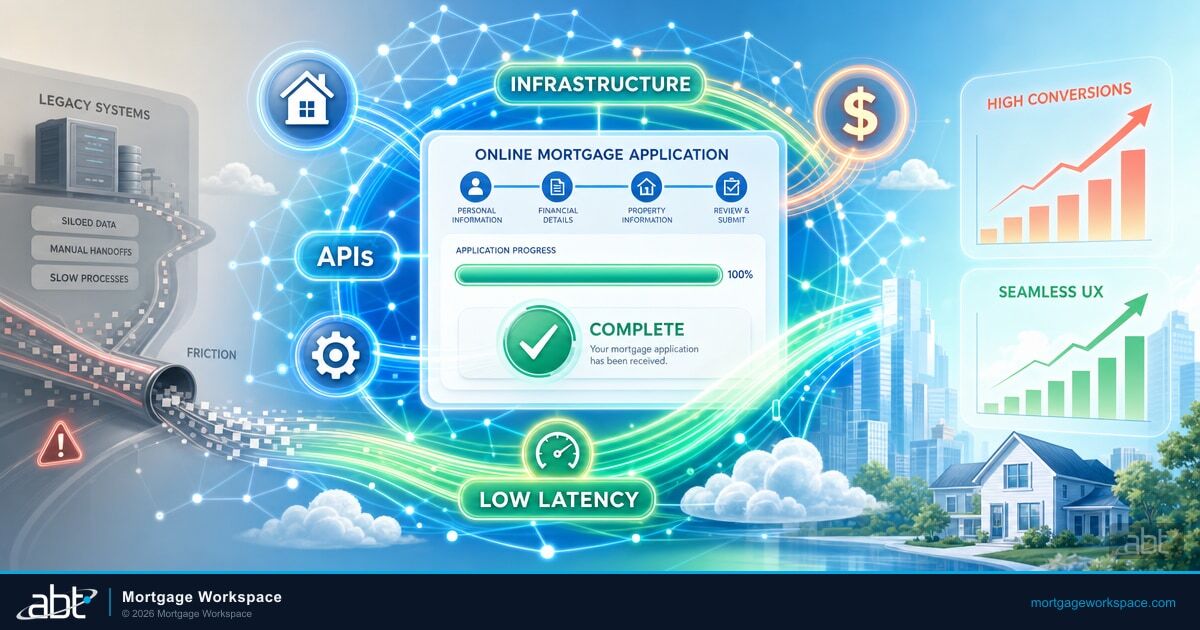
Legacy systems compound the problem. Many mortgage companies still run older on-premise servers and patchwork tools that weren't designed for modern threats.
- Outdated infrastructure — legacy software lacks modern threat detection. Patches get applied weeks late because IT teams are stretched thin
- Expanding compliance requirements — GLBA non-compliance carries penalties up to $100,000 per violation. The FTC Safeguards Rule now requires written information security programs and documented risk assessments. State-level privacy laws continue lowering their applicability thresholds
- Small IT teams — most mid-size mortgage companies have two to five IT staff handling everything from help desk tickets to security monitoring. Proactive security takes a back seat to daily firefighting
The Managed Security Alternative
When your IT team has two people handling everything from password resets to compliance audits, something always falls through the cracks. A mortgage-focused managed service provider handles the security configuration, monitoring, and incident response that internal teams can't staff for — using the same Microsoft 365 tools you already license.
Microsoft 365 Security Features That Protect Mortgage Data
Microsoft 365 Business Premium and E5 licenses include security tools that replace or exceed what most mortgage companies get from separate vendors:
| Tool | What It Does | Mortgage-Specific Impact |
|---|---|---|
| Defender for Office 365 | AI-driven detection of phishing, malware, and impersonation | Stops wire fraud emails targeting mortgage closings before they reach inboxes |
| Data Encryption | Encrypts all data at rest and in transit | Borrower loan files stay encrypted even when downloaded to local devices |
| MFA | Second verification step beyond passwords | Blocks 99%+ of credential attacks — even if a loan officer's password is phished |
| Conditional Access | Rules-based access by location, device, and risk | Blocks sign-ins from unmanaged devices, untrusted locations, or foreign countries |
| Purview DLP | Detects and blocks sensitive data from leaving the org | Catches SSNs and credit reports in emails, Teams, and now images via OCR |
| OneDrive/SharePoint | Encrypted cloud storage with granular permissions | Replaces local file servers with access-controlled, ransomware-recoverable storage |
These tools work as layers. Defender catches external threats. MFA prevents stolen credentials from being useful. Conditional Access limits where data can travel. DLP catches accidental exposure. OneDrive and SharePoint replace vulnerable local file servers with encrypted, permission-controlled storage. One license, layered defense.
Find Out Where Your M365 Security Stands Today
A free assessment shows which security features you already have and what needs hardening.
Built-In Compliance Tools for Mortgage Regulations
Mortgage companies subject to GLBA, FTC Safeguards Rule, and state regulations benefit from compliance tools already included in their Microsoft 365 license:
Without M365 Compliance Tools
- Manual spreadsheets to track regulatory posture
- Hours spent assembling documents for audit requests
- Inconsistent retention — some files kept too long, others deleted too soon
- No answer when auditors ask who accessed a borrower file
With M365 Compliance Tools
- Compliance Manager scores your posture against GLBA and NIST
- eDiscovery searches and exports records in seconds with chain of custody
- Retention policies enforce TRID's 3-year requirement automatically
- Audit logs answer "who, what, when" for every file access in seconds
For a deeper look at how Microsoft 365's full suite maps to mortgage workflows, see our complete M365 guide. For compliance-specific dashboards, see how Power BI templates turn compliance requirements into real-time monitoring.
Implementation Roadmap for Mortgage Companies
Deploying Microsoft 365 security isn't a single project. It's a sequence of steps, each building on the one before:
8-Week Security Deployment Roadmap
- Week 1-2: Enable MFA for all users. No exceptions for executives or part-time staff.
- Week 2-3: Configure Conditional Access. Block legacy authentication. Require managed devices for borrower data.
- Week 3-4: Deploy DLP policies for SSNs, account numbers, and credit report data. Start in audit mode, then enforce.
- Week 4-6: Activate Defender. Enable Safe Links, Safe Attachments, and anti-phishing policies. Run a phishing simulation baseline.
- Week 6-8: Set up Compliance Manager and retention policies. Map regulatory requirements to M365 controls.
- Ongoing: Review Secure Score weekly. Monthly access reviews. Update DLP policies as regulations change.

Your Microsoft 365 license already includes the security tools you need. The question isn't whether you can afford to deploy them — it's whether you can afford not to, with 739 financial services breaches in a single year.
A Tier-1 Microsoft CSP can audit your current environment, configure these controls, and provide ongoing monitoring — so your two-person IT team doesn't have to become full-time security specialists.
750+ Financial Institutions Trust Their M365 Security to ABT
Mortgage Workspace configures and manages Microsoft 365 security for credit unions, banks, and mortgage companies nationwide. We handle the setup, monitoring, and incident response so your team stays focused on lending — not chasing security alerts.
Frequently Asked Questions
Microsoft 365 Business Premium and E5 include controls that map directly to GLBA and FTC Safeguards Rule requirements. These include data encryption at rest and in transit, multi-factor authentication, data loss prevention policies, audit logging, and Compliance Manager for tracking regulatory posture. A qualified managed service provider configures these controls to meet mortgage-specific compliance needs.
Microsoft Defender for Office 365 uses AI-driven analysis to detect phishing emails, malicious attachments, and impersonation attempts before they reach inboxes. Safe Links rewrites URLs to check them at click time. Safe Attachments detonates files in a sandbox before delivery. Anti-phishing policies detect domain spoofing and display name impersonation targeting mortgage wire transfers and closing documents.
Microsoft Purview Data Loss Prevention automatically detects sensitive information like Social Security numbers and bank account details in emails, documents, and Teams messages. It blocks or flags content before it leaves your organization. Purview now includes OCR scanning that catches sensitive data in images and PDFs. Mortgage companies need DLP to prevent accidental data exposure and meet GLBA requirements for safeguarding borrower information.
A complete Microsoft 365 security deployment for a mid-size mortgage company takes 6 to 8 weeks following a phased approach. MFA and Conditional Access deploy in the first two weeks. DLP policies and Defender configuration follow in weeks three through four. Compliance Manager setup and retention policies complete the deployment. Ongoing monitoring and tuning continue beyond the initial implementation.

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch has spent over 25 years securing Microsoft 365 environments for financial institutions. As CEO of Access Business Technologies, the largest Tier-1 Microsoft Cloud Solution Provider dedicated to financial services, he manages security configurations for more than 750 banks, credit unions, and mortgage companies — helping them turn their existing M365 licenses into layered defenses against the threats targeting borrower data.