In This Article
In the first half of 2025, Darktrace observed 2.4 million phishing emails targeting financial sector customers. Nearly 30% aimed at VIP users. Mortgage companies sit squarely in that crossfire. Every loan file holds Social Security numbers, bank statements, and tax returns. Attackers know this. They are getting faster, smarter, and more persistent.
Point-in-time security checks miss what happens between audits. A stale account goes unnoticed for six weeks. An employee skips MFA registration. A Conditional Access policy gets disabled during a troubleshooting session and never gets re-enabled. These gaps compound quietly until an attacker finds one.
Continual monitoring closes those gaps before they become incidents. And in an industry where regulatory timelines are tightening by the quarter, the window for "good enough" security is closing fast.
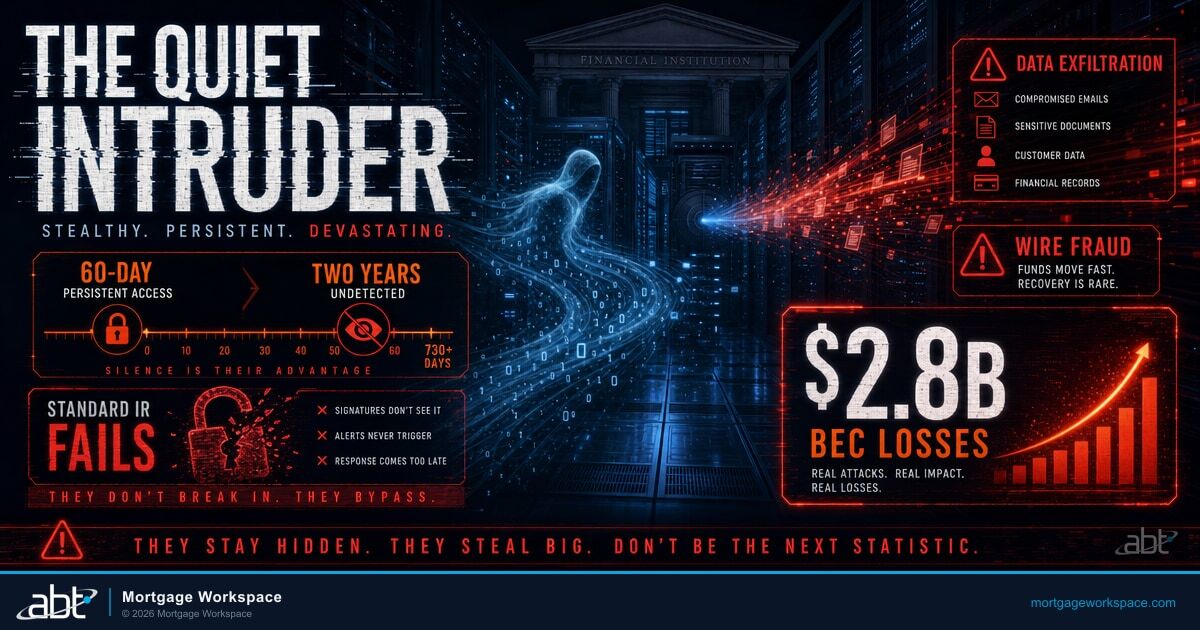
The Detection Gap
The global average time to detect and contain a data breach is 241 days, according to IBM's 2025 Cost of a Data Breach Report. That means an attacker who compromises a mortgage company's environment in January might not be discovered until August. For an industry handling sensitive financial data under strict regulatory timelines, 241 days is an eternity.
Why a High Secure Score Hides Real Risks
The average Microsoft Secure Score across all organizations falls between 30% and 45%. Most mortgage companies that ABT encounters on first assessment sit below 40%. But here is the uncomfortable truth: even companies that push their score to 75% or higher can still be wide open to attack.
Microsoft Secure Score measures whether a policy is configured. It does not measure whether that policy is actually enforced, whether users completed enrollment, or whether someone quietly disabled it last Tuesday during a troubleshooting call.
Here are the four gaps Secure Score hides:
- MFA registration gaps. 90% of organizations have MFA "enabled." Only 41% enforce it. Microsoft shows a green checkmark on the policy. It does not flag the users who never completed enrollment. Those accounts are one phished password away from compromise.
- Stale accounts and orphaned access. Roughly 15% of privileged accounts sit dormant for 180+ days. Former employees, shared mailboxes, and service accounts that nobody owns create backdoors that credential stuffing attacks walk right through.
- Configuration drift. IT teams disable a Conditional Access policy to troubleshoot. Nobody re-enables it. Microsoft tracked 176,000 configuration drift incidents in a single month across its customer base. The Secure Score might not drop because the policy still "exists" on paper.
- Human error compounds everything. 82% of cloud misconfigurations come from human error, not software flaws. Between 23% and 31% of all cloud breaches trace back to misconfiguration. A single manual change - an exclusion added, a setting toggled - can undo months of hardening work overnight.
Secure Score is a starting point. It is not proof that your environment is actually protected. The gap between what a dashboard says and what an attacker sees is exactly where breaches happen. For a deeper look at what those gaps cost in real dollars, see The Hidden Costs of IT Complexity in Mortgage Operations.

| What Secure Score Shows | What It Misses | The Real Risk |
|---|---|---|
| MFA policy enabled ✓ | 41% of orgs don't enforce enrollment | 99% of compromises hit non-enforced accounts |
| Conditional Access configured ✓ | 176K drift incidents/month across Microsoft | Policy bypasses accumulate silently |
| Device compliance set ✓ | Unmanaged devices bypass CA entirely | Shadow endpoints outside your perimeter |
| Score: 75% ✓ | 15% of privileged accounts dormant 180+ days | Credential stuffing backdoors |
| All policies "active" ✓ | 82% of misconfigs from human error | 23-31% of cloud breaches from misconfig |
What Continual Monitoring Looks Like in Practice
ABT built Guardian Security Insights to go beyond what Microsoft surfaces by default. It pulls data from your Microsoft 365 tenant every night. No manual scripts. No digging through nested admin menus.
The result is a set of prioritized findings your IT team can act on immediately:
- Users who have MFA "enabled" but never registered. This is the single most common hidden risk in mortgage company tenants. Guardian flags them by name.
- Devices not enrolled in Intune. Unmanaged endpoints bypass your Conditional Access policies entirely.
- Accounts inactive for 30, 60, or 90 days. Stale accounts are low-hanging fruit for credential stuffing attacks.
- External sharing anomalies. Who shared what, with whom, and when. DLP violations surface automatically.
Every finding comes with a recommended action. No guesswork.
The gap between what your security dashboard shows and what an attacker actually sees is where breaches live. Continual monitoring closes that gap every 24 hours.
The Compliance Pressure Is Accelerating
HUD's Mortgagee Letter 2024-10 requires FHA lenders to report significant cybersecurity incidents within 12 hours of detection. The Mortgage Bankers Association noted this timeline creates real operational challenges, especially for smaller lenders still assessing an incident's scope.
Fannie Mae published its Information Security and Business Resiliency Supplement with requirements effective August 2025. Sellers and servicers must maintain a formal InfoSec program aligned with NIST standards, report cyber breaches within 36 hours, and provide annual officer attestation across 14 security domains.
The FTC Safeguards Rule requires continuous monitoring or annual penetration testing plus semi-annual vulnerability scans. The NYDFS Part 500 amendments made universal MFA mandatory by November 2025, with $250,000 per-day fines for ongoing non-compliance.
You cannot meet these deadlines with quarterly spot-checks. Continual monitoring is the only way to know your actual posture at any given moment. For a breakdown of how strong cybersecurity posture becomes a competitive differentiator, see our companion article on turning security into a business advantage.
Key Compliance Deadlines Mortgage Companies Cannot Miss
HUD ML 2024-10: 12-hour incident reporting for FHA lenders - effective now.
Fannie Mae ISBRS: Annual InfoSec attestation across 14 domains, 36-hour breach reporting - effective August 2025.
FTC Safeguards Rule: Continuous monitoring or annual pentest + semi-annual vuln scans - effective now.
NYDFS Part 500: Universal MFA mandatory, $250K/day fines for non-compliance - effective November 2025.
How Mason-McDuffie Mortgage Transformed Their Security Posture
Mason-McDuffie Mortgage (MasonMac) started with a Microsoft Secure Score of 32%. Manual checks and custom PowerShell scripts overwhelmed their IT team. Critical gaps went undetected for months.
After implementing Guardian Security Insights, MasonMac saw measurable results:
- Secure Score improved from 32% to over 90% within six months
- IT identified users who appeared MFA-protected but had never completed registration
- Monthly executive reports gave leadership clear visibility into security progress
- Nightly automated data pulls replaced manual PowerShell scripts
Clinton Weyland, VP of IT at MasonMac, said:
Guardian Security Insights gave us the visibility and insights we needed to make informed decisions quickly. The continual monitoring and regular reports were game-changers for our IT team and leadership.
What Would Nightly Monitoring Uncover in Your Tenant?
MasonMac went from a 32% Secure Score to over 90% in six months. The first step was seeing what manual checks were missing.
What Guardian Security Insights Delivers
Guardian Security Insights is part of ABT's Guardian operating model. It sits on top of your existing Microsoft 365 environment and extracts signal that native tooling misses. ABT serves 750+ financial institutions with this approach.
Nightly Automated Pulls
Data comes directly from your tenant. No agents to install. No third-party platforms. ABT runs a pure Microsoft stack.
BI-Style Dashboards
IT teams get prioritized to-do lists. Executives get board-ready summaries. Both views come from the same data set.
Historical Trend Tracking
See how your posture improved month over month. Prove ROI to your board. Show examiners a documented trajectory.
Deeper MFA Analysis
Standard Microsoft reports show policy status. Guardian shows actual enrollment, completion rates, and at-risk accounts that fall through the cracks. Learn more about the executive perspective on Guardian and why leadership visibility changes the security conversation.
Your 90-Day Monitoring Action Plan
Whether you implement Guardian or build your own monitoring practice, here is a practical timeline:

Days 1-30: Visibility
We recommend starting with these steps: Deploy nightly data pulls from your M365 tenant. Start by identifying every user, device, and policy in your environment. Catalog MFA registration status, device enrollment gaps, and stale accounts. Establish your baseline Secure Score and document what it misses.
Days 31-60: Remediation
Close the gaps your baseline assessment uncovered. Based on our experience across 750+ institutions: Enforce MFA registration for every account. Disable stale accounts. Enroll unmanaged devices in Intune. Fix Conditional Access policy exclusions. Track progress weekly against your baseline.
Days 61-90: Governance
Build recurring reporting for IT and executive leadership. Set thresholds for automatic alerts on configuration drift. Document your monitoring process to create examiner-ready evidence. Establish the cadence that keeps your posture from regressing.
Frequently Asked Questions
Periodic assessments capture a snapshot on a single day. Continual monitoring pulls data from your Microsoft 365 tenant every night, detecting configuration drift, new stale accounts, and MFA registration gaps as they appear. This daily cadence means your IT team acts on findings within hours instead of discovering problems weeks or months later during an audit.
The FTC Safeguards Rule requires non-banking financial institutions, including mortgage lenders, to implement continuous monitoring of their information systems or conduct annual penetration testing combined with semi-annual vulnerability scans. Mortgage companies must also designate a Qualified Individual, maintain a written incident response plan, and report breaches affecting 500 or more consumers to the FTC within 30 days of discovery.
Periodic assessments and static scores capture a point-in-time snapshot but miss configuration drift that occurs between reviews, newly created stale accounts from employee turnover, MFA registrations that were started but never completed, and conditional access policy exclusions added as temporary fixes that become permanent gaps. Continual monitoring detects these changes within 24 hours of occurrence, which is critical because attackers scan for exactly these kinds of transient vulnerabilities.
ABT's Guardian Security Insights connects directly to your existing Microsoft 365 tenant. There are no agents to install and no third-party platforms to configure. Most mortgage companies begin receiving nightly automated reports within the first week. The full Guardian hardening process, which addresses the vulnerabilities those reports surface, typically runs as a 90-day sprint.
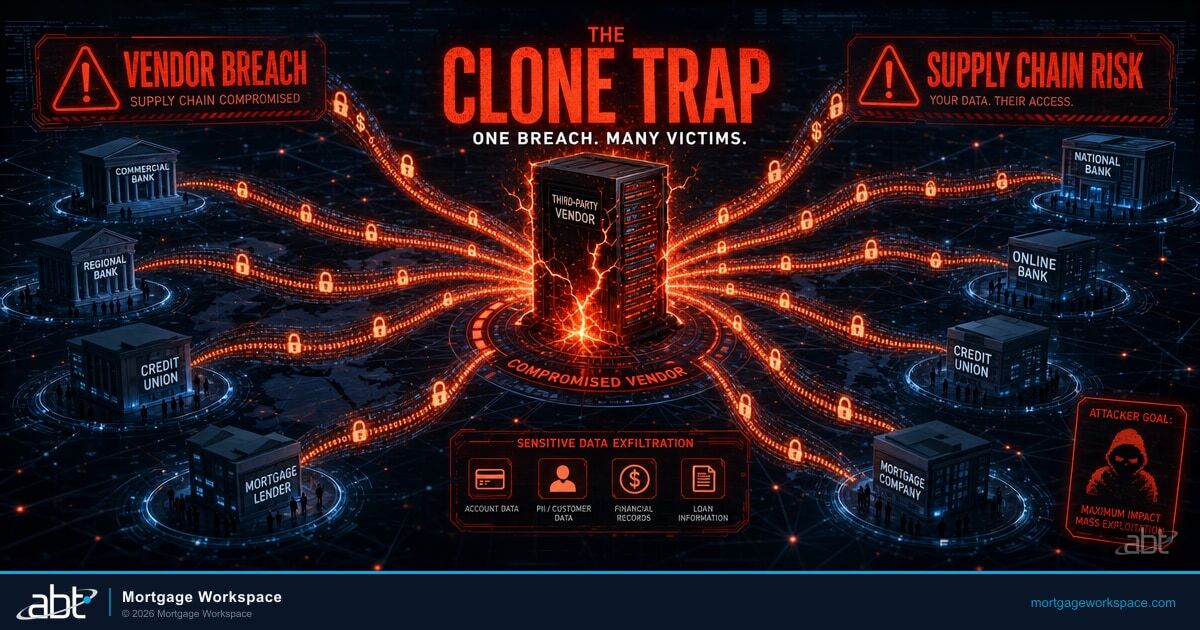
In August 2025, Marquis Software Solutions suffered a ransomware attack that exposed Social Security numbers, tax identification numbers, and financial account information belonging to customers of over 700 financial institutions. The vendor paid the ransom, triggering OFAC sanctions considerations and FinCEN SAR filing requirements for every affected institution. The breach demonstrated how a single third-party vendor compromise can cascade across hundreds of organizations simultaneously.
Stop Guessing. Start Monitoring.
Cyber threats against mortgage companies increased 20% year over year in 2025. Regulators are tightening reporting windows. Fannie Mae now mandates annual InfoSec attestation. ABT has served 750+ financial institutions with Guardian Security Insights - the same approach that took MasonMac from a 32% Secure Score to over 90%.

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch designed ABT's continual monitoring approach after seeing mortgage companies pass annual audits and then get breached three months later. As CEO of Access Business Technologies, he built Guardian Security Insights to close the gap between point-in-time assessments and the daily configuration drift that attackers actually exploit - protecting more than 750 financial institutions with nightly automated security scans.