In This Article
- What Infrastructure-First Means for Mortgage Companies
- The Azure Foundation: Where the Mortgage Stack Actually Lives
- Why Software-First Approaches Keep Failing
- The Five Infrastructure Layers Mortgage Lenders Need
- M365 Guardian: The Governance Layer Over the Stack
- Measuring Infrastructure Maturity
- How to Start the Infrastructure-First Shift
- Frequently Asked Questions
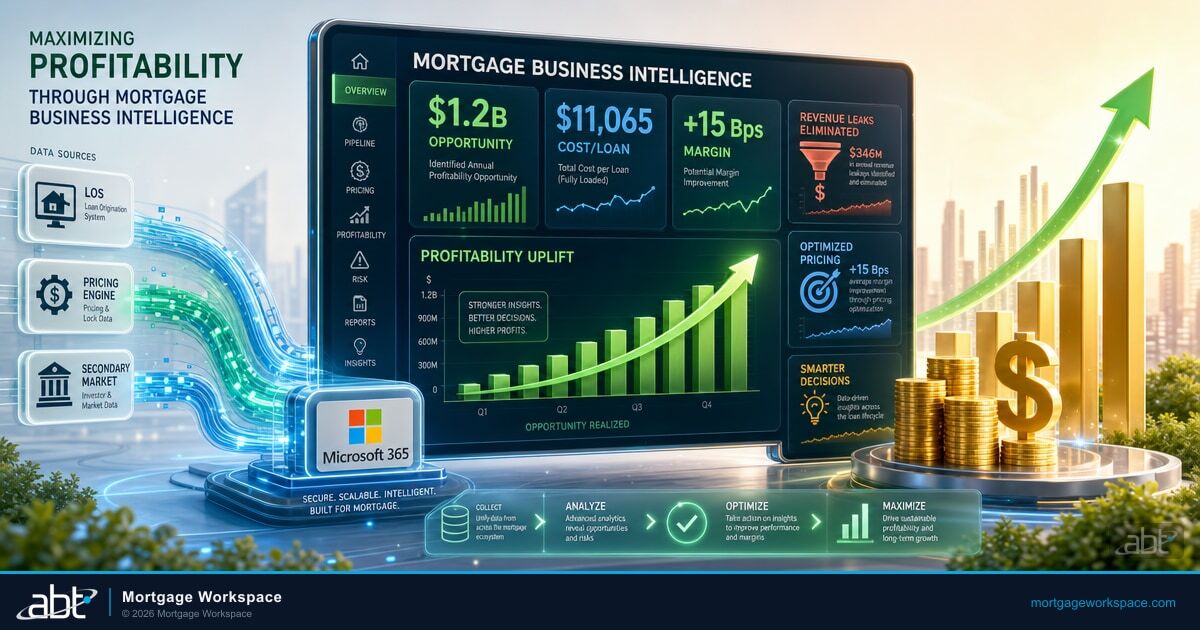
Technology now accounts for 10-18% of operating expenses at large mortgage lenders, yet less than 10% have the infrastructure resources to scale operations cleanly. MBA projects single-family originations to reach $2.2 trillion in 2026, up 8% from 2025. Lenders are spending accordingly. Financial institutions nearly quadrupled their tech spend per $1 billion in assets between 2022 and 2024, rising from $200K to $780K. But the spend keeps going into software while the foundation that software needs goes unbuilt.
The disconnect is structural. Lenders keep buying loan origination systems, point-of-sale platforms, customer engagement tools, and compliance dashboards while ignoring the identity, network, data, and hosting layers those tools sit on top of. The result is slow systems, failed integrations, compliance gaps, and per-loan costs that eat margins. Access Business Technologies operates Microsoft 365 tenants and Azure environments for 750+ financial institutions, and the pattern recurs across nearly every mortgage company that walks in carrying a stack-rationalization problem.
This article explains what mortgage IT infrastructure actually includes, why software-first approaches fail, and how an infrastructure-first stack built on Microsoft Azure (operated by ABT), tied together by MortgageExchange, anchored by Calyx PointCentral on a dedicated Azure subscription, and governed by M365 Guardian produces a foundation that every software tool you add can actually use.
What Infrastructure-First Means for Mortgage Companies
Infrastructure-first means building the technology foundation before selecting or deploying software tools. For mortgage companies, that foundation covers identity management, network architecture, endpoint security, data governance, monitoring, and the cloud environment where the production workload actually runs. Every LOS, POS, CRM, and compliance tool runs on this foundation.
A loan origination system is only as good as the network it runs on, the identity controls that protect it, the cloud hosting that keeps it available, and the monitoring that catches problems before borrowers do. Software is the visible layer. Infrastructure is everything that makes the visible layer work, and the part that examiners, auditors, and the firm's CFO all hold accountable when something breaks.
Consolidated Analytics captured this shift in its 2026 mortgage tech outlook: AI becomes core infrastructure, and integrated systems win. Both statements depend on infrastructure maturity. AI cannot function without clean, governed data pipelines. Integration cannot work without standardized APIs, consistent authentication, and reliable connectivity between the LOS and the lender's core banking system.
The Azure Foundation: Where the Mortgage Stack Actually Lives
Mortgage infrastructure has to live somewhere. For ABT customers, the somewhere is Microsoft Azure, hosted by ABT as the partner of record. The Azure subscription is customer-owned cloud infrastructure that ABT operates day to day, which means the lender keeps the regulatory relationship with Microsoft while ABT runs the workload inside it. That distinction matters for examiner conversations about third-party oversight, and it matters for the firm's CFO because the Azure environment scales up or down with origination volume instead of forcing capital expenditure on on-premise servers that get under-utilized in a slow quarter.
On top of that Azure foundation, two ABT-built layers turn raw cloud capacity into an actual mortgage operating environment. The first is MortgageExchange, the data layer that connects the LOS to the lender's core banking system. Most mortgage technology breaks down at the integration seam between origination and servicing or between origination and the bank or credit union's core. MortgageExchange is the custom interface that runs the cadence integrations, the file moves, the boarding routines, and the field mappings that keep both sides consistent. It is the reason a mortgage company on ABT can post a closed loan to the core in minutes instead of overnight.
The second is Calyx PointCentral, hosted on a dedicated Azure subscription that ABT operates for each lender. PointCentral is the loan origination platform the lender's loan officers, processors, and underwriters use every day, and the dedicated-subscription model is what keeps one lender's environment isolated from every other lender's environment at the hosting layer. ABT operates the subscription, applies the patches, runs the backups, and produces the audit evidence that regulators look for under FFIEC and GLBA. The lender runs the loans. That is the infrastructure-first split: ABT owns the foundation, the lender owns the business.
The Infrastructure-First Mortgage Stack
- Microsoft Azure (ABT-hosted) is the cloud foundation. The customer's Azure subscription is operated by ABT under the partner-of-record relationship. Capacity scales with volume.
- MortgageExchange is the data layer. It connects the LOS to the core banking platform and runs the cadence integrations that keep origination and servicing consistent.
- Calyx PointCentral on a dedicated Azure subscription is the loan origination workload. One lender per subscription means tenant isolation at the hosting layer, not just at the application layer.
- Microsoft 365 (ABT-managed) sits above the workload. Microsoft hosts the M365 infrastructure; ABT manages the tenant via delegated admin. That is where Entra ID identity, Intune device management, Defender threat protection, and Purview retention live.
- M365 Guardian is the operating model that ties the layers together. It is what turns a collection of Microsoft products into a continuously governed mortgage environment.
Why Software-First Approaches Keep Failing
The Mortgage Collaborative's president, Jodi Hall, made it plain at MBA 2025: lenders spent the first half of 2025 ripping out technology they bought during COVID. The buying spree created overlapping tools, redundant capabilities, and integration headaches. The correction is still underway.
Integration Fails Without a Data Layer
A Wolters Kluwer survey of 110 mortgage executives found that 69% plan to invest in new or upgraded LOS platforms. But a new LOS sitting on fragmented infrastructure still cannot talk to the POS, the CRM, the document management system, the compliance tools, or the core banking platform. Without a data layer like MortgageExchange running standardized integrations, every new tool becomes its own silo. The lender ends up paying for ten products that each work in isolation and none of which talk to each other.
AI Underwriting Fails Without Data Governance
Only 7% of mortgage leaders are actively deploying AI, despite 65% reporting familiarity with the technology. The gap is not about awareness. It is about data readiness. AI underwriting models need clean, governed, accessible data to produce accurate results. If borrower data lives in disconnected systems with inconsistent formats, the model produces garbage. Microsoft Purview, applied consistently across the M365 tenant by ABT, creates the data classification and retention foundation AI requires. Without that foundation, no Copilot deployment is going to land.
Compliance Tools Cannot Compensate for Architectural Gaps
Mortgage compliance operates across GLBA, CFPB, FTC Safeguards Rule, FFIEC guidelines, and state-level requirements. Compliance software tracks and reports. If the underlying infrastructure does not enforce access controls through Microsoft Entra ID, maintain audit logs through Microsoft Purview, encrypt data properly through Azure-native disk and Microsoft 365 service encryption, and segment sensitive workloads at the hosting layer, the compliance tool is reporting on a broken foundation. Buying more compliance software does not fix that gap.
Scaling Breaks What Was Not Built to Scale
MBA forecasts 8% origination growth in 2026. When volume increases, infrastructure gaps become operational crises. Slow networks create bottleneck queues. Overloaded identity systems lock out loan officers. Storage that was not sized for growth forces expensive emergency expansions. An ABT-hosted Azure environment scales up the underlying compute and storage with volume, so the LOS does not hit a wall the week after rates drop and applications spike.
The Five Infrastructure Layers Mortgage Lenders Need
Layer 1: Identity and Access Management
Every person and system that touches borrower data needs a managed identity. That means centralized authentication through Microsoft Entra ID, multi-factor authentication on every account, role-based access control matched to job function, and automated offboarding that revokes access the same day someone leaves. ABT manages the Entra ID configuration inside the Microsoft 365 tenant for every customer, which means MFA enforcement, Conditional Access policies, and Privileged Identity Management run the same way across the lender's footprint instead of branch-by-branch.
Identity also covers service accounts used by LOS integrations, API connections to credit bureaus, and the automated workflows that move borrower documents between systems. Every credential is tracked, rotated, and auditable.
Layer 2: Network Architecture and Connectivity
Mortgage workflows depend on reliable connectivity between loan officers, processors, underwriters, title companies, appraisers, and investors. Network architecture has to support both in-office and remote work with consistent performance. That includes SD-WAN for branch connectivity, zero-trust network access for remote workers, and dedicated bandwidth between the lender's offices and the ABT-hosted Azure environment where the LOS workload lives.
Layer 3: Endpoint Security and Management
Mortgage data flows through laptops, desktops, and mobile devices. Every endpoint is a potential entry point for attackers. Microsoft Intune enrollment, managed by ABT inside the M365 tenant, ensures devices meet compliance baselines, stay patched, and run approved software. Microsoft Defender for Endpoint catches threats that prevention misses. The combination is what lets a loan officer work from a coffee shop without putting borrower data at risk.
Layer 4: Data Governance and Protection
Borrower data classification, encryption policies, retention schedules, and data loss prevention rules form the governance layer. This is not a project you do once. It is an operating practice that adapts as regulations change. GLBA requires safeguards for nonpublic personal information. The FTC Safeguards Rule sets specific technical requirements. State rules like NYDFS add additional mandates. Microsoft Purview is the layer inside the M365 tenant that meets those bars, and ABT manages the configuration so the policies apply uniformly across mailboxes, SharePoint sites, OneDrive accounts, and Teams chats.
Layer 5: Monitoring, Alerting, and Response
Infrastructure without monitoring is infrastructure you find out about from borrowers or regulators, not from your own team. Microsoft Sentinel aggregates signals from Entra ID, Defender, Purview, and the Azure-hosted LOS workload into one incident view. ABT's security operations runs the alerting and the response playbooks. The lender keeps focused on closing loans instead of triaging firewall logs.
M365 Guardian: The Governance Layer Over the Stack
An infrastructure-first stack still drifts. Conditional Access policies get edited locally. New branches come online with default tenant settings. Devices arrive from a regional supplier and never get enrolled. None of this is malicious. It is the natural drift of a federated mortgage operation that has not put a continuous governance layer in place.
M365 Guardian is ABT's operating model that closes that drift. Guardian is not another product line bolted on top of Microsoft 365. It is the way ABT runs the Microsoft 365 tenant for a regulated financial services firm. Guardian includes mortgage-specific Conditional Access policies tuned to branch geography and loan officer behavior, mortgage-specific Data Loss Prevention rules for borrower NPI and credit data, retention policies aligned to GLBA and FFIEC expectations with documented testing, Communication Compliance review templates calibrated to mortgage regulatory findings, a Microsoft Sentinel deployment tuned to mortgage attack patterns rather than generic SMB defaults, and the 24/7 security operations center that watches the Sentinel and Defender signals every minute of the day.
The point is not that Guardian is the only governance approach. The point is that a Microsoft 365 tenant managed by a generalist IT shop without an operating model on top of it produces inconsistent baselines, missed alerts, and exam findings the lender would rather not see. Guardian is the layer that turns the infrastructure stack into a continuously governed environment instead of a configuration that drifts until the next examination cycle catches up with it.
Software is the visible layer. Infrastructure is what makes the visible layer work. Guardian is what keeps the infrastructure inside the operating envelope every regulator already expects.
Measuring Infrastructure Maturity
You cannot manage what you do not measure. The metrics that matter for a mortgage company's infrastructure posture:
| Metric | What It Tells You | Target |
|---|---|---|
| Identity coverage | Percentage of systems behind centralized authentication through Microsoft Entra ID | 100% |
| Patch currency | Days between patch release and deployment to endpoints | Under 14 days for critical patches |
| Endpoint compliance | Percentage of devices meeting Microsoft Intune compliance baselines | Above 95% |
| Mean time to detect (MTTD) | Time between a security event and the team knowing about it | Under 1 hour |
| Audit readiness | Time to produce GLBA, FTC Safeguards, or FFIEC evidence on examiner request | Under 24 hours |
How to Start the Infrastructure-First Shift
Step 1: Audit what you have. Map every system, connection, identity, and data flow. Most mortgage companies discover they have more tools, more identities, and more data stores than they realized. The audit is also the place to find out how many of those systems are sitting on infrastructure the firm cannot describe.
Step 2: Identify the gaps. Compare the current state against the five infrastructure layers. Where are credentials unmanaged? Where is data unencrypted? Where does monitoring not reach? Where is the LOS running on a server in a closet whose backup tape has not been tested since 2022?
Step 3: Prioritize by risk. Fix identity and access first. It is the foundation everything else depends on. Then address endpoint security, then data governance, then monitoring. Move the LOS to a hosted environment before the next exam cycle.
Step 4: Build before you buy. Before evaluating any new software tool, confirm the infrastructure can support it. Can the network handle the bandwidth? Can the identity system manage the integration? Can MortgageExchange carry the new data flow? Can the Azure environment scale to the load?
ABT builds mortgage technology environments from the infrastructure up. We host the Azure foundation, run MortgageExchange as the data layer, host Calyx PointCentral on a dedicated Azure subscription per lender, manage the Microsoft 365 tenant, and apply M365 Guardian as the governance layer on top. For mortgage companies that have spent the past two years buying software and watching it fail to deliver, the infrastructure-first stack is the reset.
Get a Mortgage Infrastructure Review
ABT runs the infrastructure-first stack described in this article for mortgage companies operating across multiple branches, affiliated entities, and remote loan officer footprints. A 30-minute conversation maps your current LOS, integration, and hosting posture, surfaces the gaps your next exam cycle is most likely to find, and outlines what an ABT-managed deployment would cover. No commitment, no quote, no obligation.
Key Takeaway
Mortgage technology has to start with infrastructure. The Azure foundation, hosted by ABT and scaled with origination volume, carries the workload. MortgageExchange ties the LOS to the lender's core banking system. Calyx PointCentral runs on a dedicated Azure subscription per lender. Microsoft 365 sits above the workload with Entra ID identity, Intune endpoint management, Defender threat protection, and Purview data governance, all managed by ABT inside the customer's tenant. M365 Guardian is the operating model that keeps the whole stack inside the envelope examiners expect. Software purchases stop being a string of disconnected bets and start being capabilities that ride on a foundation built to carry them.
For more on how the data layer ties this together, see our companion article on how mortgage software integration reduces operational bottlenecks. For the API and integration architecture detail, read how API-driven mortgage software builds the client experience and mortgage software integration with cloud technology.
Frequently Asked Questions
Infrastructure-first means building identity management, network architecture, endpoint security, data governance, monitoring, and the cloud hosting environment before selecting or deploying software tools. Every loan origination system, point-of-sale platform, and compliance tool depends on this foundation. For ABT customers, the foundation is Microsoft Azure operated by ABT as the partner of record, with MortgageExchange running the data integrations and Calyx PointCentral hosted on a dedicated Azure subscription per lender. Without that foundation, software purchases create silos, integration failures, and compliance gaps that cost more to fix than to prevent.
Software-first fails because tools need infrastructure to function properly. Without a data layer like MortgageExchange running the integrations between the LOS and the core banking platform, new systems cannot talk to existing ones. Without Microsoft Purview governing the data, AI and analytics produce unreliable results. Without Microsoft Entra ID managing identity, compliance tools report on a broken foundation. The 2025 wave of mortgage companies ripping out COVID-era tech purchases illustrates the pattern: software bought on top of fragmented infrastructure does not deliver, regardless of how good the software is on its own.
The five layers are identity and access management through Microsoft Entra ID, network architecture and connectivity, endpoint security and management through Microsoft Intune and Microsoft Defender for Endpoint, data governance and protection through Microsoft Purview, and monitoring with alerting and response through Microsoft Sentinel. These layers support every software tool a mortgage company deploys. Building them in order, starting with identity, creates a foundation that scales with loan volume and adapts to regulatory changes. ABT manages every one of these layers inside the customer's Microsoft 365 tenant under the M365 Guardian operating model.
The dedicated-subscription model means each lender's PointCentral environment is isolated at the hosting layer, not just at the application layer. ABT hosts the subscription on Microsoft Azure as the partner of record, applies the patches, runs the backups, and produces the audit evidence that regulators look for under FFIEC and GLBA. The lender keeps tenant ownership and the regulatory relationship with Microsoft. One lender per subscription keeps capacity, security, and recovery scoped per customer instead of pooled across many.
MortgageExchange is the data layer that connects the LOS to the lender's core banking system and to the other systems in the mortgage stack. Most mortgage technology breaks down at the integration seam between origination and servicing, or between origination and the bank or credit union's core. MortgageExchange runs the cadence integrations, the file moves, the boarding routines, and the field mappings that keep both sides consistent. It is the reason a mortgage company on ABT can post a closed loan to the core in minutes instead of overnight, and it is the layer that makes additional software purchases (POS, CRM, document management) actually integrate instead of becoming standalone silos.
M365 Guardian is ABT's operating model for running the Microsoft 365 tenant of a regulated mortgage company. It includes mortgage-specific Conditional Access policies, Data Loss Prevention rules tuned to borrower NPI and credit data, retention policies aligned to GLBA and FFIEC, Communication Compliance review templates calibrated to mortgage regulatory findings, a Microsoft Sentinel deployment tuned to mortgage attack patterns, and the 24/7 security operations center that watches the Sentinel and Defender signals around the clock. Guardian is the layer that keeps the infrastructure inside the envelope examiners expect, so the lender does not have to assemble configuration evidence by hand the week before a cycle exam opens.

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch has helped mortgage companies, banks, and credit unions modernize their technology since 1999. As CEO of Access Business Technologies, the largest Tier-1 Microsoft Cloud Solution Provider dedicated to financial services, he helps more than 750 institutions build infrastructure-first technology stacks on Microsoft Azure and Microsoft 365, integrate origination and servicing through MortgageExchange, and meet examiner expectations through the M365 Guardian operating model.