In This Article
- Quick Recap: Where Complexity Hides
- Case Study: From Fragmented to Centralized
- Building Transparency Into IT Operations
- Accountability Through Automated Reporting
- How the M365 Guardian Operating Model Fits
- Microsoft Purview as the Records Backbone
- Why a Tier-1 Microsoft Direct-Bill CSP Anchors the Plan
- Your 90-Day Action Plan
- Frequently Asked Questions
In Part 1, the breakdown covered how IT complexity silently drains mortgage operations. Tool sprawl. Manual data transfers. Compliance gaps from inconsistent records. MBA data from Q3 2025 puts the average cost to originate a mortgage at $11,109 per loan, roughly 42 percent above the long-term historical average since 2008, and fragmented IT environments are a major contributor.
This is Part 2. Here, the article walks through what fixing that complexity looks like in practice, with a real case study, concrete steps, and a 90-day timeline a mortgage operator can follow. The fix anchors on three things: Microsoft 365 as the single platform of record, the M365 Guardian operating model that ABT layers on top of it, and a Tier-1 Microsoft Direct-Bill CSP relationship that puts one operational owner in front of the whole stack.
Quick Recap: Where Complexity Hides
Three costs compound when mortgage IT systems do not talk to each other:
- Labor waste: 70 percent of lending professionals spend 20 or more hours per week navigating disconnected platforms.
- Maintenance drag: Custom integrations break with every vendor update, pulling IT staff away from security and strategic work.
- Compliance exposure: Inconsistent data across LOS, CRM, and document systems creates audit risk under GLBA and the FTC Safeguards Rule.
What Changed in 2025 to 2026
The FFIEC officially sunset its Cybersecurity Assessment Tool (CAT) on August 31, 2025. Financial institutions must now use NIST CSF 2.0, CRI Profile, or CIS Controls for maturity assessments. If a mortgage company's security posture still depends on fragmented tools without a unified framework mapping, that gap just got harder to explain to examiners.
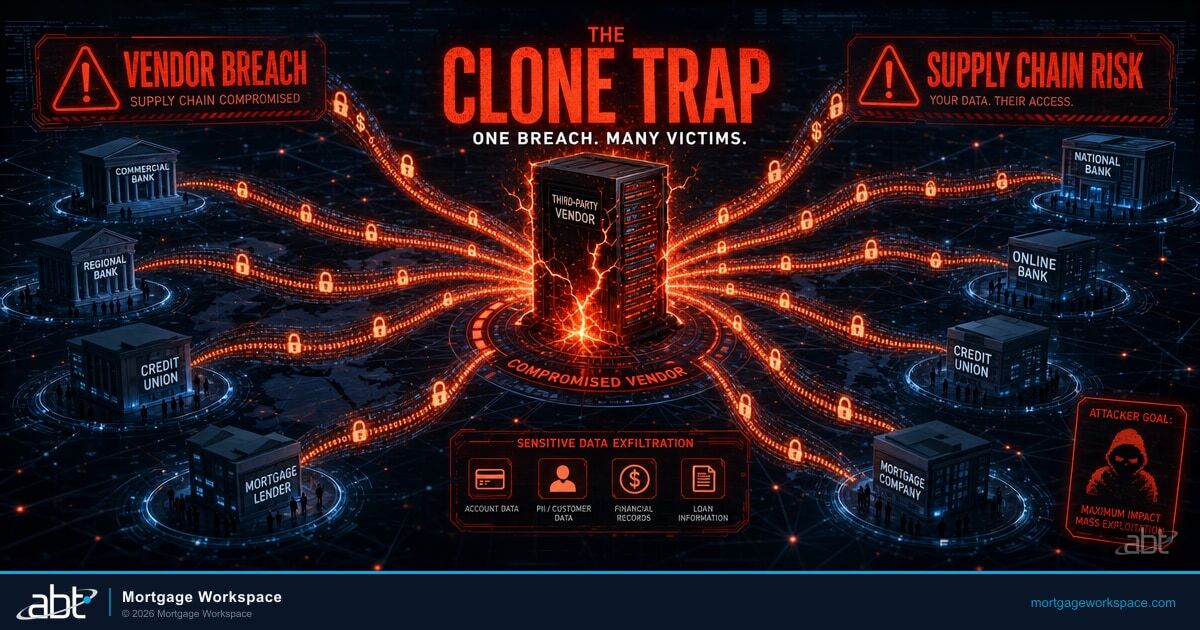
The 2025 WEF Global Cybersecurity Outlook found that 54 percent of large organizations cite supply chain and vendor complexity as their biggest barrier to cyber resilience. For mortgage companies juggling a dozen platforms, that finding hits close to home.
Case Study: From Fragmented to Centralized
A mid-size mortgage company with over 1,000 user accounts and nearly 2,000 managed devices came to MortgageWorkSpace after a costly incident. On paper, their IT looked robust: multiple security tools, endpoint protection on most devices, and MFA turned on for most accounts.
The gaps told a different story:
- 200 or more devices running outdated operating systems.
- 15 percent of accounts with incomplete MFA enrollment.
- Dozens of stale accounts still active months after employees left.
- No single view of security posture across the organization.
Their CFO clicked a phishing email on one of those unpatched devices. Attackers stole an MFA token and accessed the company's financial systems.
Wire transfers exceeding $1 million were initiated before anyone noticed. This was not a failure of any single tool. It was a failure of complexity. Too many disconnected systems, too many gaps between them, and too few people with visibility into all of it.
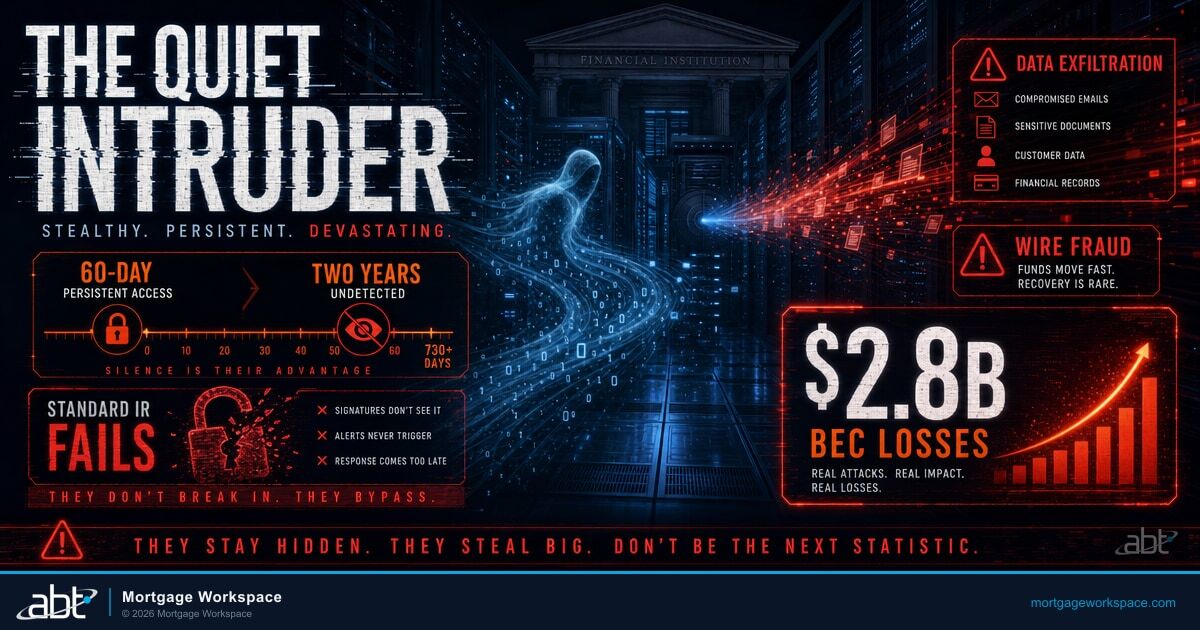
This pattern is not unusual. The OCC disclosed in April 2025 that a single compromised admin account in its on-premises Exchange environment exposed approximately 150,000 sensitive emails from 103 executive and examiner accounts, and the activity went undetected for 20 months. When fragmented systems lack centralized monitoring, breaches have time to compound.
How Would Your Tenant Hold Up?
The case study above started with a single unpatched device. A 15-minute security assessment shows a mortgage operator exactly where the gaps are before attackers find them.
Building Transparency Into IT Operations
After the incident, ABT helped this company rebuild with a different approach. Instead of adding more tools, the engagement connected the ones they already had through one Microsoft 365 tenant under delegated administration.
The first step was consolidation:
Before: Fragmented Stack
- 5 separate security dashboards.
- Manual MFA enrollment tracking.
- No automated stale account cleanup.
- Patch status unknown across endpoints.
- Microsoft Secure Score in the low 30s.
After: Centralized on Microsoft 365
- Microsoft Defender as the single pane of glass.
- Microsoft Entra ID Conditional Access enforcing MFA on every login.
- Automated account lifecycle (30-day flag, 60-day disable).
- Microsoft Intune enforcing device compliance.
- Microsoft Secure Score above 80 within 90 days.

The Secure Score jump was measurable, but it was not the point. The point was that leadership could now see their security posture in one place, updated daily, without asking IT to run manual reports.
Microsoft reported blocking 7,000 password attacks per second in 2024, more than double the rate from 2023. Organizations relying on fragmented identity systems are the ones those attacks succeed against.
Accountability Through Automated Reporting
Visibility without accountability changes nothing. The second step was building automated reporting that made security everyone's responsibility.
The system generates weekly reports showing:
- Device compliance rates by department.
- MFA enrollment gaps with named accounts.
- Patch status across all endpoints.
- Sign-in anomalies that need investigation.
These reports go to IT, department heads, and executive leadership. When the VP of Sales sees that three loan officers have MFA gaps, they follow up directly. IT does not carry the accountability alone anymore.
The NCUA's 2026 Supervisory Priorities explicitly fold cybersecurity into operational risk management, requiring examiners to assess "effective governance, risk assessments, vendor management, and security frameworks" for payment systems and member data protection.
Automated reporting proves those capabilities exist without consuming IT hours to produce the evidence. When an examiner asks for vendor management documentation, pulling a weekly report beats scrambling to build one from five different dashboards.
How the M365 Guardian Operating Model Fits
Microsoft 365 ships with the raw controls a mortgage company needs. Microsoft Entra ID for identity. Microsoft Defender for threat detection. Microsoft Intune for device posture. Microsoft Purview for records and data governance. Microsoft Sentinel for SIEM. The gap is not the toolset. The gap is the operating model that keeps every one of those controls configured the same way across the business, monitored every hour of every day, and producing the evidence an examiner can read in a single sitting.
The M365 Guardian operating model is the ABT-owned layer that sits on top of those Microsoft controls. ABT manages the Microsoft 365 tenant under delegated administration as a Microsoft Cloud Solution Provider, and the Guardian operating model translates the Microsoft control surface into a mortgage-specific posture: identity baselines tuned to loan officer behavior, Conditional Access policies that account for branch geography and remote work patterns, Defender rules that recognize wire fraud and BEC patterns common to mortgage operations, and Purview retention policies tuned to GLBA, the FTC Safeguards Rule, and state-level licensing rules that vary by where a mortgage company holds licenses.
What the mortgage company experiences is the outcome. A consistent Microsoft 365 security baseline applied across the whole organization, not branch by branch. Continuous drift detection, surfaced inside the M365 Guardian dashboard before an examiner finds it. A documented response trail when a control falls out of policy. A single operational owner accountable for the whole stack. The CFO and the CIO see one number for the firm's posture, not five dashboards that took three weeks to reconcile.
Nightly Assessments
Automated security posture scans of the Microsoft 365 tenant, every night, no manual effort required.
Action-Prioritized Dashboards
Surface what needs attention first, so the IT and compliance teams fix the highest-risk gaps before examiners find them.
Trend Tracking
Leadership sees whether security is improving or drifting, week over week, month over month.
Compliance-Ready Reports
Pre-formatted evidence mapping to GLBA, FTC Safeguards Rule, FFIEC frameworks, and NCUA requirements.
Key Takeaway
The M365 Guardian operating model is not another tool added on top of the Microsoft 365 stack. It is the management discipline that makes the Microsoft tools the mortgage company already pays for actually pay off, with the operational accountability sitting at ABT and the regulatory accountability staying with the firm. The same approach informs how a mortgage operator should think about cloud migration broadly.
Microsoft Purview as the Records Backbone
Microsoft Purview is the layer inside Microsoft 365 that holds up the books-and-records side of a mortgage operation. Purview Audit produces the time-stamped audit log of every create, modify, and delete action across Exchange Online, SharePoint Online, OneDrive, Teams, and Microsoft Entra ID. Purview Audit Premium extends retention to one year with the option to extend to ten, which matches the practical retention floor mortgage operators face under federal recordkeeping rules and the long-tail of state licensing inquiries.
Retention policies bind tamper-evident retention to mailboxes, sites, and Teams channels where customer communications and loan files live. Purview Data Loss Prevention prevents customer NPI from leaving the tenant through unmanaged channels. Purview Information Protection labels sensitive documents so an underwriter's analysis or a borrower's appraisal carries its classification with it regardless of who opens it. Purview Communication Compliance lets the firm sample, classify, and review business communications for off-channel behavior, harassment, or policy-flagged content, which is the same surface that recurs in the FINRA Rule 3110.09 findings broker-dealer affiliates of mortgage operations face during examinations.
Within the M365 Guardian operating model, ABT applies and monitors those Purview configurations the same way across the firm's footprint, and the partner-side multi-tenant control plane produces the cross-tenant audit reports a compliance officer can hand to an examiner without building a spreadsheet by hand. The mortgage operator continues to own the records, the loan files, and the customer relationships. ABT operates the Microsoft tools that keep those records consistent and defensible.
Why a Tier-1 Microsoft Direct-Bill CSP Anchors the Plan
The 90-day plan only holds if one operational owner is accountable for every layer of the Microsoft 365 stack across the business. ABT is a Tier-1 Microsoft Direct-Bill Cloud Solution Provider, which is the partner program tier where the partner transacts directly with Microsoft, manages customer tenants under delegated administration, and is operationally accountable to Microsoft for how those tenants are configured and run. ABT manages Microsoft 365 tenants for more than 750 financial institutions, and mortgage operators are a substantial portion of that footprint.
The difference between a Tier-1 Direct-Bill CSP and a license reseller shows up in the operating model. A reseller hands over a billing relationship and walks away. A Direct-Bill CSP owns the configuration, the monitoring, the drift detection, the policy updates, and the evidence chain. The mortgage operator continues to hold the licenses and the regulatory relationship. ABT operates the Microsoft 365 tenant against the firm's policies, with delegated administrative access scoped per role and per workload, and the M365 Guardian operating model layered on top to translate the Microsoft control surface into a mortgage-specific posture.
Your 90-Day Action Plan
A year-long project is not the answer to reducing IT complexity. The following practical timeline reflects what works across hundreds of financial institutions:
Days 1 to 30: Inventory tools, map data flows, baseline Microsoft Secure Score, document gaps.
Days 31 to 60: Microsoft Entra ID with Conditional Access, Intune enrollment, stale account cleanup.
Days 61 to 90: Deploy automated reporting, weekly compliance dashboards, measurable targets.

Days 1 to 30: Audit and Baseline
- Inventory every tool, platform, and integration in the environment.
- Map data flows between systems and identify every manual transfer point.
- Run a Microsoft Secure Score assessment to establish a baseline.
- Document stale accounts, unmanaged devices, and MFA gaps.
Days 31 to 60: Consolidate and Connect
- Migrate identity management to Microsoft Entra ID with Conditional Access policies in Grant mode, not Report-Only.
- Enroll all devices in Microsoft Intune for compliance enforcement.
- Disable stale accounts and establish automated lifecycle policies.
- Connect core systems through managed APIs, including the firm's LOS, CRM, and document management platforms.
Days 61 to 90: Automate and Report
- Deploy automated security reporting to leadership.
- Establish weekly compliance dashboards inside the M365 Guardian operating model.
- Set measurable targets for Microsoft Secure Score, device compliance, and MFA coverage.
- Review progress with the Microsoft Direct-Bill CSP partner.
MBA data shows origination costs hit $11,109 per loan in Q3 2025, roughly 42 percent above the long-term average. Lenders who invest in integration and automation capture savings that fragmented operations leave on the table.
Start Your 90-Day Simplification Plan
The mortgage company in this case study went from a Microsoft Secure Score in the 30s to above 80 in 90 days. The engagement covers:
- Full environment audit with Microsoft Secure Score baseline.
- Identity consolidation roadmap on Microsoft Entra ID with Conditional Access.
- M365 Guardian operating model deployment for automated compliance reporting.
- Microsoft Purview retention and DLP configured to GLBA and FTC Safeguards Rule expectations.
- 90-day progress tracking with weekly executive dashboards.
Frequently Asked Questions
The M365 Guardian operating model is the management discipline that ABT layers on top of a mortgage company's Microsoft 365 tenant. ABT, a Tier-1 Microsoft Direct-Bill Cloud Solution Provider, manages the tenant under delegated administration and applies Microsoft Entra ID, Microsoft Defender, Microsoft Intune, Microsoft Purview, and Microsoft Sentinel against a mortgage-specific posture. The mortgage operator experiences consistent security baselines across the organization, nightly automated assessments of the tenant, drift detection across branches and remote teams, and compliance-ready reports aligned with GLBA, the FTC Safeguards Rule, FFIEC frameworks, and NCUA requirements, without paying for another stack of point tools.
A structured 90-day plan produces measurable results. The first 30 days focus on auditing the current environment and establishing baselines on Microsoft Secure Score, device compliance, and MFA coverage. Days 31 through 60 address identity consolidation on Microsoft Entra ID, Microsoft Intune device enrollment, stale account cleanup, and connection of core systems through managed APIs. The final 30 days deploy automated reporting, weekly executive dashboards inside the M365 Guardian operating model, and ongoing monitoring against measurable security and compliance targets.
Microsoft Entra ID manages identity and access with Conditional Access policies. Microsoft Intune enforces device compliance across all endpoints. Microsoft Defender for Office 365 and Microsoft Defender for Endpoint centralize threat detection and response across email and devices. Microsoft Purview handles audit logging, retention, data loss prevention, and communication compliance for the books-and-records side. Microsoft Sentinel aggregates the signals into a single incident view that supports examination evidence. Together, these tools replace multiple disconnected security and compliance products with one platform a Tier-1 Direct-Bill CSP partner can operate consistently across the firm.
Microsoft Purview is the layer inside Microsoft 365 that holds up the books-and-records side of a mortgage operation. Purview Audit produces a time-stamped audit log across Exchange Online, SharePoint Online, OneDrive, Teams, and Microsoft Entra ID. Purview Audit Premium extends retention to one year with the option to extend to ten. Retention policies bind tamper-evident retention to mailboxes, sites, and channels where loan files and customer communications live. Purview Data Loss Prevention prevents customer NPI from leaving the tenant through unmanaged channels. Purview Information Protection labels sensitive documents so the classification follows the file. Inside the M365 Guardian operating model, ABT applies and monitors these Purview configurations consistently across the firm's footprint and produces the cross-tenant audit evidence a compliance officer hands to an examiner.
Tier-1 Direct-Bill is the partner program tier where ABT transacts directly with Microsoft, manages customer Microsoft 365 tenants under delegated administration, and is operationally accountable to Microsoft for how those tenants are configured and run. The mortgage operator retains ownership of the Microsoft 365 licenses and the regulatory relationship with examiners. ABT operates the tenant against the firm's policies and applies the M365 Guardian operating model to translate the Microsoft control surface into a mortgage-specific posture. This is materially different from a license reseller arrangement, where the partner hands over a billing relationship and walks away from configuration, monitoring, and drift detection. ABT manages Microsoft 365 tenants for more than 750 financial institutions, including a substantial number of mortgage operators.
Automated reporting generates weekly or daily security posture summaries without requiring manual IT effort. Reports cover Microsoft Intune device compliance rates, Microsoft Entra ID MFA enrollment, patch status, and sign-in anomalies. Inside the M365 Guardian operating model, reports also surface Microsoft Purview retention and DLP posture, Microsoft Defender incident counts, and Microsoft Sentinel alert disposition. These reports provide audit-ready evidence for GLBA, the FTC Safeguards Rule, and FFIEC examinations while distributing accountability beyond the IT team to department heads and executive leadership.
The FFIEC officially sunset its Cybersecurity Assessment Tool on August 31, 2025. Financial institutions must now adopt alternative frameworks such as NIST CSF 2.0, CRI Profile, or CIS Controls for cybersecurity maturity assessments. There is no single mandated replacement, so institutions choose the framework that best fits their size and complexity. A Tier-1 Direct-Bill CSP partner can map the Microsoft 365 control surface against any of the three frameworks inside a single posture report, which is how the M365 Guardian operating model produces evidence that examiners accept without an additional consulting engagement.

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch has guided Microsoft deployments for regulated financial institutions since 1999. As CEO of Access Business Technologies, the largest Tier-1 Microsoft Direct-Bill Cloud Solution Provider dedicated to financial services, he helps more than 750 banks, credit unions, mortgage companies, and securities firms standardize their Microsoft 365 tenants for examination readiness without slowing down how the business actually works.