In This Article
- The 2026 Regulatory Landscape for Remote Mortgage Work
- What a Remote-Work Breach Actually Costs in 2026
- Device Security and the BYOD Problem
- Secure Communications for Distributed Teams
- Multi-State Licensing and Privacy Compliance
- Data Protection and Access Controls
- The M365 Guardian Operating Model for Remote Mortgage Teams
- Building a Compliant Remote Work Framework
- Frequently Asked Questions
The Federal Trade Commission's Safeguards Rule breach notification requirement took effect in May 2024. Mortgage companies, credit unions, and banks that experience a data breach affecting 500 or more customers must now report it to the FTC within 30 days. When your loan officers and processors work from home, every unmanaged device and unencrypted connection turns into a potential breach waiting to happen.
Remote work is not the compliance challenge. Unmanaged remote work is. And the price of getting it wrong climbed sharply in 2025. IBM's Cost of a Data Breach Report 2025 put the financial-services average at $5.56 million per incident, with the United States average across all industries reaching $10.22 million. Those numbers are the headline. The supervision findings on your next CFPB or state housing-agency examination are the consequence.
Here is what leaders at credit unions, banks, and mortgage companies need to address in 2026 to keep distributed workforces compliant, productive, and defensible. Access Business Technologies manages Microsoft 365 tenants for more than 750 financial institutions, and the operating pattern that surfaces clean exams in this environment has a name: M365 Guardian, the ABT operating model layered over Microsoft Entra ID, Microsoft Intune, Microsoft Defender, and Microsoft Purview.
The 2026 Regulatory Landscape for Remote Mortgage Work
Multiple regulatory frameworks govern how financial institutions handle data in remote work environments. Most have tightened materially since 2024. The ones a mortgage IT leader has to know cold:
- GLBA (Gramm-Leach-Bliley Act): Requires financial institutions to protect consumer financial data and implement written information security programs. Annual penetration tests and semiannual vulnerability scans are now baseline expectations under the FTC Safeguards Rule.
- FTC Safeguards Rule: Covers 13 categories of financial businesses, explicitly including mortgage lenders, brokers, and servicers. The 2023 amendments added mandatory encryption, access controls, MFA, and continuous monitoring. The 2024 breach-notification trigger requires reporting to the FTC within 30 days of discovering unauthorized acquisition of customer information affecting 500 or more consumers (16 CFR Part 314.5).
- NYDFS 23 NYCRR Part 500 Second Amendment: Phased compliance dates rolled in on November 1, 2023, November 1, 2024, and November 1, 2025. As of 2026, every obligation is in force for covered entities, including any New York-licensed mortgage lender or servicer.
- State privacy laws: The 2024-2026 window brought a dozen new state privacy regimes into force. They do not replace GLBA, but they apply to mortgage data outside the GLBA carve-out (marketing data, vendor management records, employee data, and certain business-to-business contexts).
- GSE requirements: Fannie Mae and Freddie Mac impose additional cybersecurity and data handling standards on approved sellers and servicers, with annual attestations and incident reporting expectations that mirror the federal framework.
If your institution is licensed in New York, the NYDFS amendments are particularly important. The Second Amendment expects a designated, qualified Chief Information Security Officer reporting to the board, a written incident response plan, MFA across privileged and remote access, risk-based vulnerability management, and a 72-hour reporting clock for material cybersecurity events. That clock is shorter than the FTC's 30-day Safeguards Rule clock, and the two run independently. A New York-licensed lender with a breach affecting California borrowers and Texas employees may be juggling three different reporting timelines.
The Three-Clock Problem in Remote Mortgage Compliance
A single incident can simultaneously trigger the FTC Safeguards 30-day clock, the NYDFS 72-hour clock, and individual state breach-notification clocks (some as short as 30 days from discovery). Your written incident response plan needs to assume all three fire on the same incident. The remote worker who clicks the phishing link in Reno on a Tuesday afternoon can put your CISO in front of three regulators by Friday.

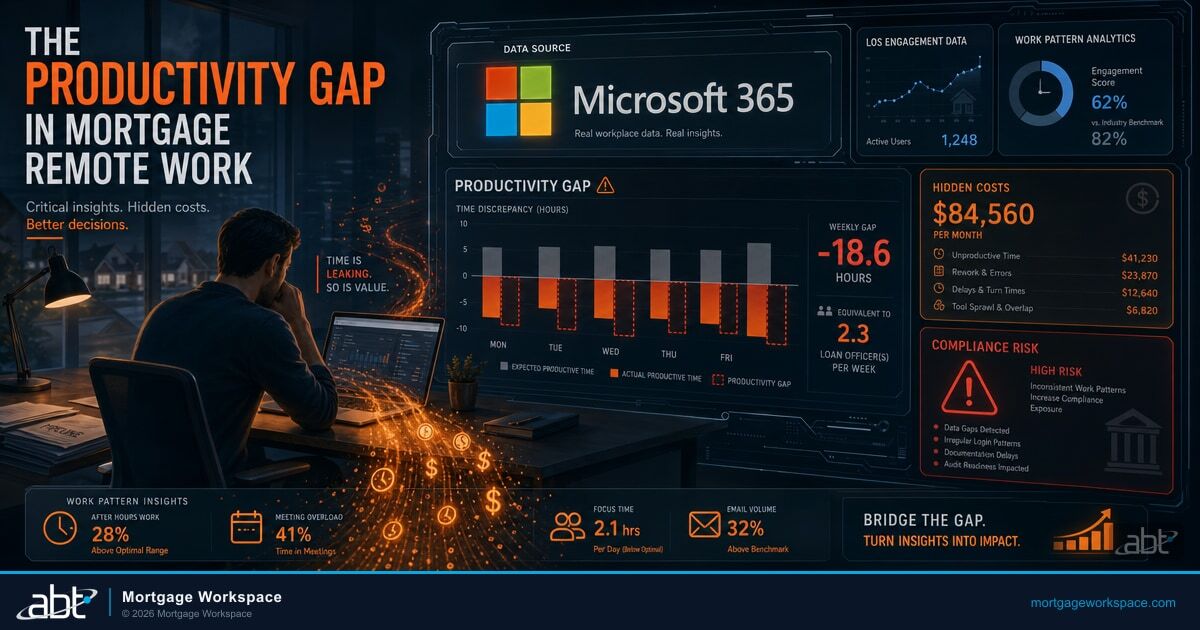
What a Remote-Work Breach Actually Costs in 2026
The cost calculation has shifted enough that the old "we can absorb a small incident" reasoning no longer holds. IBM's 2025 report breaks the financial picture down with painful clarity:
- $5.56 million is the average cost of a financial-services breach (third-highest of any industry; covers banks, credit unions, insurance, payments, and mortgage operators)
- $10.22 million is the average cost in the United States across all industries, the highest regional figure in the report
- $4.44 million is the global average across all industries
The mortgage industry sits squarely in the financial-services bucket. The breach is rarely "the hack" itself. It is the federal and state notification costs, the credit monitoring offers to affected borrowers, the regulator examination follow-up, the GSE counterparty review, and the reputational drag on origination volume for the following two quarters. Our analysis of DLP technology in mortgage compliance walks through exactly how unmanaged channels become the entry point for these incidents.
The financial-services breaches we see during pre-onboarding assessments at credit unions, community banks, and mortgage companies almost always trace back to identity gaps and unmanaged endpoints rather than missing perimeter tools. Microsoft Entra ID Conditional Access, Microsoft Intune device compliance, Microsoft Defender for Office 365 anti-phishing, and Microsoft Purview Data Loss Prevention close the four most common attack paths when configured against the FTC Safeguards Rule remote-work sub-requirements. Most institutions already hold the licenses inside Microsoft 365 Business Premium or E3+E5 stacks; the gap is configuration, monitoring, and enforcement, not procurement. That is the configuration and monitoring work ABT performs as the Tier-1 Direct-Bill CSP that manages the Microsoft 365 tenants for more than 750 financial institutions, under the M365 Guardian operating model.
Device Security and the BYOD Problem
Personal devices remain the single biggest compliance risk in remote mortgage work. A loan officer processing applications on a personal laptop that lacks disk encryption, endpoint protection, and managed updates creates exposure that no policy document can fix. The FTC Safeguards Rule mandates specific technical controls that BYOD complicates:
- Encryption of customer information both in transit and at rest on any device used for work
- Multi-factor authentication for accessing systems containing customer data
- Access controls that limit each employee to only the customer information they need for their role
- Monitoring of authorized user activity to detect unauthorized access or use
Microsoft Intune and Microsoft Entra ID Conditional Access address this directly. Intune enforces device-compliance standards before granting access. Conditional Access verifies every login attempt against pre-defined criteria including device health, location, sign-in risk, and user identity. For mortgage companies that allow BYOD, Microsoft recommends App Protection Policies (Mobile Application Management, or MAM) as the modern path: work data stays protected inside approved applications without requiring full device enrollment. Borrower data stays encrypted and managed even on personally owned phones and tablets.
Define the device-compliance baseline first
Disk encryption, supported OS version, current patch level, no jailbreak/root, screen-lock policy, antivirus running. Without this baseline, every other control floats. Microsoft Intune compliance policies enforce these requirements and report non-compliant devices to Microsoft Entra ID, which can then block access through Conditional Access.
Decide BYOD or no-BYOD before you write the policy
If BYOD is allowed, App Protection Policies are the right primary control. If BYOD is prohibited, Intune device enrollment plus Conditional Access "require compliant device" is cleaner. Mixing the two without clarity creates audit findings.
Inventory every device that touches borrower data
Every laptop, every phone, every tablet, including the personal device the regional manager occasionally checks email on. The Intune device list plus Microsoft Entra ID sign-in logs gives you the answer. If a device shows up in sign-in logs but not the Intune list, that is a finding waiting to be discovered by an examiner.
Secure Communications for Distributed Teams
Compliance requires that all communications containing customer financial data use encrypted channels. That sounds simple. In practice, remote workers default to whatever is convenient.
Common violations we see at credit unions, banks, and mortgage companies during pre-onboarding assessments:
- Sharing loan documents through personal email accounts
- Discussing borrower details on unencrypted messaging apps
- Storing customer files in personal cloud storage (Dropbox, Google Drive personal accounts)
- Taking screenshots or photos of sensitive documents on personal devices
- Sending unencrypted PDFs to title companies, real estate agents, or co-borrowers who are not on the institution's secure document portal
The fix is a combination of policy and technology. Microsoft Teams with compliance recording and Microsoft Purview Data Loss Prevention policies prevents sensitive data from leaving approved channels. SharePoint with Microsoft Purview Information Protection sensitivity labels ensures documents are classified and protected based on content. Microsoft 365 Message Encryption and Mail Flow rules add a second layer for outbound email to external parties.
Policy alone will not work. People take shortcuts. Technology that blocks the shortcuts before they happen is the only reliable control.
For practitioners building this out: our deeper write-up on bridging IT and compliance with Microsoft solutions walks through the configuration order for Microsoft Purview, Microsoft Defender, and Microsoft Entra ID so the controls reinforce each other instead of fighting each other.
Need a baseline read on your remote-work exposure?
ABT's Microsoft 365 Security Grade scores Conditional Access, Intune compliance, Purview DLP, and MFA coverage against the FTC Safeguards Rule in about 15 minutes.
Multi-State Licensing and Privacy Compliance
Remote work creates a multi-state compliance puzzle that did not exist when everyone worked in the same office. When a loan officer works from her home in Nevada but processes loans for borrowers in California, both states' regulations apply. When the same officer takes a vacation in Florida and processes a single loan from a hotel room, the licensing exposure follows her.
Key multi-state considerations in 2026:
- Licensing requirements: Most states require mortgage loan originators to be licensed in the state where the borrower is located. Remote work does not change this. But it does create scenarios where originators inadvertently work outside their licensed states. Document where each licensed originator is physically working when they touch a loan file.
- State privacy laws: The 2024-2026 window brought a wave of new state privacy regimes. Most have GLBA carve-outs for financial-institution data, but mortgage marketing data, employee records, and vendor relationships often fall outside the carve-out. The chart below covers the ones most likely to touch a mortgage operation with multi-state remote workers.
- Tax implications: Employees working remotely from different states trigger nexus and withholding requirements. Your accounting team needs to track where each employee primarily works, and your IT logs (Microsoft Entra ID sign-in locations) often become the audit evidence the tax authorities ask for.
- Supervision requirements: State regulators expect that remote workers receive the same level of supervision as in-office staff. That means documented oversight processes, not just occasional check-ins. CFPB examination priorities for 2026 explicitly call out supervisory adequacy for remote loan originators.

Twelve states activated comprehensive consumer privacy laws between July 2024 and January 2026: Texas (TDPSA, July 2024), Oregon (OCPA, July 2024), Florida (FDBR, July 2024), Montana (October 2024), Delaware, Nebraska, New Hampshire, and Iowa (all January 2025), Tennessee (TIPA, July 2025), Minnesota (MCDPA, July 31, 2025), Maryland (MODPA, October 2025), and Indiana (January 2026). California's privacy regime continues to operate under the California Privacy Rights Act (CPRA), which superseded the original CCPA in 2023. Tracking which laws apply to which data flows is the kind of work that benefits from automated compliance monitoring rather than spreadsheets and quarterly check-ins. Our piece on data-driven compliance dashboards using Power BI walks through one approach.
Data Protection and Access Controls
The principle of least privilege applies to every remote worker. Loan processors should access only the files they are actively working. Branch managers should see only their branch's data. No one needs blanket access to the entire document repository from their home office.
Implementing proper access controls in a remote environment requires:
- Role-based access policies: Define what each job function can access and enforce it through your identity management system
- Conditional Access rules: Restrict sensitive data access based on device compliance, network location, sign-in risk signals, and session controls
- Session timeouts: Automatically lock sessions after periods of inactivity to prevent unauthorized access on unattended devices
- Audit logging: Record who accessed what, when, and from where. This data is required for GLBA compliance and invaluable during FTC, NYDFS, CFPB, and state housing-agency examinations
Microsoft Entra ID (formerly Azure Active Directory) combined with Microsoft Purview provides the identity governance and data classification framework most mortgage compliance programs need. Microsoft Purview Audit (Premium) gives a default 1-year retention for Exchange Online, SharePoint, OneDrive, and Microsoft Entra ID audit records, with extended-retention policies running up to 10 years using the 10-Year Audit Log Retention add-on. Examiners do not care that the logs are inconvenient to query; they care that the logs exist and can be produced on request.
Key Takeaway for IT Leaders
In 2026, the audit log retention question is no longer "do we have logs?" It is "can we produce 12, 36, or 84 months of logs in response to a specific data-subject or examiner request?" Default Microsoft Purview Audit retention is 1 year. If your retention policy is silent, your default is 1 year. NYDFS Part 500 Second Amendment expects you to be able to defend that decision. GLBA expects you to be able to reconstruct the trail of who accessed what.
The M365 Guardian Operating Model for Remote Mortgage Teams
Distributed mortgage operations need more than a stack of Microsoft licenses. They need an operating model that applies those licenses consistently across every loan officer's home office, every branch, every affiliated entity, and every personal phone that touches borrower data. M365 Guardian is ABT's operating model for that work. Lighthouse and the Microsoft Cloud Solution Provider relationship are the access layer. Guardian is what ABT does inside that access to keep a federated mortgage operation defensible to an FTC examiner, an NYDFS regulator, and a Fannie Mae counterparty review at the same time. The mortgage company keeps its Microsoft 365 licensing and retains its tenant ownership. The Guardian layer is added through the Tier-1 Direct-Bill CSP partner relationship.
For a remote mortgage team, the Guardian layer breaks into four operating columns that map cleanly onto the FTC Safeguards Rule sub-requirements. Microsoft Entra ID supplies the identity column: Conditional Access policies enforced in Grant mode (not Report-Only) for every loan officer, processor, underwriter, and operations user; sign-in risk policies that step up MFA when a session originates from an unfamiliar country, network, or device; Privileged Identity Management (PIM) on the admin accounts that touch tenant configuration; legacy authentication blocked by default. Microsoft Intune supplies the device column: full enrollment for firm-owned laptops with the device-compliance baseline described earlier, App Protection Policies (Mobile Application Management) for personal phones used to check email, and a compliance state that feeds back into Conditional Access so a device that drifts out of compliance loses access before it loses data. Microsoft Defender for Office 365 and Defender for Endpoint supply the detection column: anti-phishing, Safe Attachments, Safe Links, and endpoint detection and response signals aggregated into Microsoft Sentinel for a unified incident timeline. Microsoft Purview supplies the recordkeeping and governance column: Audit Premium retention extended to match the institution's longest examination lookback, Data Loss Prevention policies that block borrower NPI from leaving approved channels, Information Protection sensitivity labels classifying loan packages and underwriting workpapers, Communication Compliance review templates tuned to FTC, NYDFS, and CFPB examination patterns rather than vendor SMB defaults.
The pattern that surfaces clean examinations is the same pattern across all four columns: the configuration is applied uniformly across every tenant in the firm's footprint, drift is detected continuously inside the CSP partner's multi-tenant console, and the audit evidence is in a form a CCO can hand to an examiner without spending three weeks pulling screenshots. That is the operational difference between a remote mortgage team that defends a Safeguards Rule examination cleanly and one that takes a finding for inconsistent control application. ABT performs this work for more than 750 financial institutions, layered on top of the Microsoft 365 tenants ABT manages under the Tier-1 Direct-Bill CSP relationship.
Building a Compliant Remote Work Framework
Compliance for remote mortgage teams is not a one-time project. It is an ongoing practice that requires technology, policy, and monitoring working together.
- Document your remote work security program. The FTC Safeguards Rule requires a written information security program. Update it to explicitly cover remote work scenarios, including the device-compliance baseline, the BYOD decision, the encryption requirements, and the data-handling rules for each role.
- Deploy endpoint management. Every device that touches customer data must be managed, patched, and monitored. Microsoft Intune handles this for both company-owned and BYOD devices, with App Protection Policies covering the BYOD path.
- Implement DLP policies. Prevent sensitive data from leaving approved channels through Microsoft Purview Data Loss Prevention automated detection and blocking. Cover email, Microsoft Teams, SharePoint, OneDrive, and endpoint copy-paste behaviors.
- Configure Conditional Access correctly. Require compliant device, MFA, and acceptable sign-in risk for all access to systems containing borrower data. Block legacy authentication. Apply session controls for high-risk access patterns.
- Enforce audit log retention. Set explicit Microsoft Purview Audit retention policies. The default 1-year retention is the minimum starting point; many institutions need longer retention to defend examination requests that look back further.
- Train your team. Annual security training is the minimum. Quarterly refreshers on remote-specific risks (home Wi-Fi, family member access, shared workspaces, public Wi-Fi behavior) keep compliance top of mind.
- Test your controls. Annual penetration tests and semiannual vulnerability scans are FTC Safeguards Rule requirements, not suggestions. Make sure the test scope explicitly covers remote access infrastructure.
An IT services provider serving 750+ financial institutions builds and maintains these frameworks daily. ABT knows how GLBA, the FTC Safeguards Rule, NYDFS Part 500, state privacy laws, and GSE expectations intersect with remote work technology, and the firm's M365 Guardian operating model is the configuration order that gets the controls reinforcing each other instead of fighting each other.
"The credit unions, community banks, and mortgage companies that pass their FTC Safeguards examinations cleanly are not the ones with the most policy documents. They are the ones whose Microsoft 365 Conditional Access, Intune compliance, and Purview DLP configurations match what the policy says. Examiners read the policy, then ask to see the configuration. The gap between the two is where most findings live."
Serving 750+ financial institutions since 1999
Ready to make your remote work environment compliant and defensible?
Start with a security grade, then talk to a mortgage IT specialist about closing the gaps between policy and configuration before your next examination. ABT applies the M365 Guardian operating model across Microsoft Entra ID, Microsoft Intune, Microsoft Defender, and Microsoft Purview for more than 750 financial institutions.
Frequently Asked Questions
Remote mortgage workers must comply with GLBA data protection requirements, the FTC Safeguards Rule for information security programs (16 CFR Part 314), the NYDFS 23 NYCRR Part 500 Second Amendment (phased compliance dates Nov 1, 2023 / 2024 / 2025), state-specific privacy laws including the CPRA and the 2024-2026 wave of new state regimes (Texas TDPSA, Maryland MODPA, Minnesota MCDPA, Indiana CDPA, and others), and GSE cybersecurity standards from Fannie Mae and Freddie Mac. The 2024 FTC breach notification requirement mandates reporting data breaches affecting 500 or more customers within 30 days. NYDFS imposes a separate 72-hour clock for material cybersecurity events.
Mortgage companies secure personal devices through Microsoft Intune App Protection Policies (Mobile Application Management) that protect work data within approved applications without requiring full device enrollment. Microsoft Entra ID Conditional Access policies verify device compliance, multi-factor authentication, sign-in risk, and user identity before granting access to systems containing borrower data. The FTC Safeguards Rule mandates encryption of customer information both in transit and at rest on any device used for work.
M365 Guardian is ABT's operating model layered on top of the Microsoft 365 tenants that ABT manages for more than 750 financial institutions as a Tier-1 Direct-Bill Cloud Solution Provider. For a remote mortgage operation, the Guardian layer applies Microsoft Entra ID Conditional Access, Microsoft Intune device compliance, Microsoft Defender for Office 365 and Endpoint, and Microsoft Purview Audit Premium and Data Loss Prevention policies uniformly across every loan officer, branch, and affiliated entity. The mortgage company keeps its Microsoft 365 licensing and retains its tenant ownership; the Guardian operating model is added through the partner relationship and produces the configuration consistency, drift detection, and audit evidence that FTC Safeguards Rule, NYDFS Part 500, and CFPB examiners look for.
Multi-state compliance risks for remote mortgage work include loan officers inadvertently working outside their licensed states, the 2024-2026 wave of new state privacy laws imposing different data protection requirements outside the GLBA carve-out (Texas TDPSA, Maryland MODPA, Minnesota MCDPA, Tennessee TIPA, Indiana CDPA, and others), tax nexus and withholding obligations triggered by remote employees in multiple states, and varying supervision requirements that mandate documented oversight processes for distributed workers. CFPB examination priorities for 2026 explicitly include supervisory adequacy for remote loan originators.
The FTC Safeguards Rule requires mortgage companies to maintain written information security programs covering remote work scenarios, implement encryption for customer data in transit and at rest, enforce multi-factor authentication for system access, apply role-based access controls, monitor authorized user activity, conduct annual penetration testing plus semiannual vulnerability scans covering remote access infrastructure under 16 CFR Part 314.4(d), and report data breaches affecting 500 or more customers within 30 days under 16 CFR Part 314.5. The 2023 amendments added mandatory encryption, MFA, and continuous monitoring obligations.
Mortgage companies handle Data Loss Prevention for remote teams by deploying Microsoft Purview Data Loss Prevention policies that automatically detect and block sensitive data from leaving approved channels, applying Microsoft Purview Information Protection sensitivity labels to classify documents based on content, restricting file sharing to company-managed Microsoft 365 platforms, and blocking personal email and cloud storage uploads of customer financial information through Microsoft Entra ID Conditional Access and endpoint policies. DLP covers email, Microsoft Teams, SharePoint, OneDrive, and endpoint copy-paste behaviors.
The IBM Cost of a Data Breach Report 2025 (released July 2025) put the average data breach cost for the financial services industry at $5.56 million, the third-highest of any industry. The US average across all industries was $10.22 million, and the global all-industry average was $4.44 million. The financial-services figure covers banks, credit unions, insurance, payments, and mortgage operators as a combined sector. The headline cost rarely reflects the complete impact: regulator follow-up, credit monitoring offers, GSE counterparty reviews, and reputational drag on origination volume can extend the financial exposure for two to four quarters beyond the initial incident.

Justin Kirsch
CEO, Access Business Technologies
Justin Kirsch has guided Microsoft deployments for regulated financial institutions since 1999. As CEO of Access Business Technologies, the largest Tier-1 Microsoft Cloud Solution Provider dedicated to financial services, he helps more than 750 banks, credit unions, mortgage companies, and securities firms standardize their Microsoft 365 tenants for examination readiness without slowing down how the business actually works.